Vendor risk — the exposure that comes from every third party with access to your systems, data, or operations — has become one of the most significant categories of operational risk for regulated businesses. DORA’s ICT third-party risk requirements, ISO 27001’s supplier security controls, and NIS2’s supply chain obligations all reflect the same reality: the risks your suppliers carry are risks your organisation inherits. This guide compares eight of the leading risk management software vendors and risk management platforms in 2026, with particular attention to identifying the best risk management platforms for regulated businesses seeking to strengthen their risk management program. As cyber risk continues to drive regulatory scrutiny and operational threats, evaluating the right risk management platform is essential for effective third-party oversight.
Organizations are increasingly turning to third-party risk management software platforms to centralize vendor data and automate assessments.
What Is Vendor Risk Management Software?
Vendor risk management (VRM) software, also known as third-party risk management (TPRM) software, is widely used by financial services organizations and compliance officers to identify, assess, monitor, and manage third-party and supplier risk throughout the vendor lifecycle. TPRM software supports the creation and maintenance of a comprehensive vendor inventory and automates approval workflows for onboarding, risk assessments, compliance checks, and issue resolution, ensuring structured and transparent decision-making. It centralises vendor records, risk assessments, security questionnaires, vendor security questionnaires, contractual documentation, and vendor compliance data, replacing the fragmented approach of spreadsheets and email chains that most organisations rely on at the point where third-party relationships start to scale.
Modern TPRM platforms consolidate risk assessments, inherent and residual risk scoring, framework mapping, and remediation workflows into a single system of record. They enable ongoing visibility into third-party risk by centralizing assessment results, due diligence data, and performance indicators over time. TPRM software automates evidence collection, risk tracking, and risk reporting, and maintains detailed audit trails to support audit preparation and regulatory compliance. Automated reporting and integrated risk intelligence feeds provide real-time updates on cyber risk, compliance, and supplier risk, while risk thresholds, risk processes, and risk intelligence are managed and monitored continuously. Approval workflows, audit trails, and automated reporting streamline audit preparation and compliance management. Vendor security questionnaires and security questionnaires are streamlined and tracked within the platform, supporting efficient onboarding and ongoing risk assessments.
Effective TPRM software reduces vendor-related regulatory breaches, operational disruption, and reputational damage by enabling ongoing oversight, earlier intervention, and scalable, automated processes for continuous risk monitoring.
Automate Vendor Risk Management
Copla simplifies third-party risk assessments, automating the process to reduce your workload
Types of Risk Management Software
Risk management software comes in several specialized forms, each designed to address different aspects of organizational risk:
- Vendor Risk Management Software: Focuses on identifying, assessing, and mitigating risks associated with third-party vendors. This type of software centralizes vendor data, automates risk assessments, and supports continuous monitoring of vendor risk throughout the entire vendor lifecycle. It is essential for organizations that need to manage vendor risk, ensure compliance, and maintain audit readiness.
- Third Party Risk Management Software: Encompasses a broader scope, covering all external parties—including suppliers, partners, and service providers. Party risk management software provides tools for risk assessment, ongoing monitoring, and compliance management across a wider range of third party relationships, not just contracted vendors.
- Enterprise Risk Management Software: Offers a comprehensive risk management solution that spans all risk categories within an organization, including operational, financial, strategic, and compliance risks. Enterprise risk management platforms integrate risk data from multiple sources, support continuous monitoring, and enable organizations to manage risk holistically.
Key features across these software types often include automated risk assessment, compliance management, continuous monitoring, and reporting tools. Selecting the right risk management software depends on the organization’s risk profile, regulatory requirements, and the complexity of its third party and vendor relationships.
What to Look For
DORA ICT third-party register compliance
For EU financial institutions, the ICT third-party register required by DORA is not an optional best practice — it is a supervisory expectation. Maintaining a comprehensive vendor inventory is essential for DORA compliance, as the register must document ICT service providers, the functions they support, the contractual arrangements in place, and the risk assessments that underpin those arrangements. VRM platforms that support DORA-specific register formats and documentation requirements reduce the work of satisfying that obligation substantially. Features such as audit trails and audit preparation in these platforms help organizations demonstrate regulatory compliance during supervisory inspections by providing transparent records and automating evidence collection. Generic VRM tools that require significant customisation to produce DORA-compliant documentation create more work than they save.
Continuous monitoring vs. point-in-time assessment
The annual vendor questionnaire model is increasingly inadequate. A vendor’s security posture can change in hours — a breach, a configuration change, a key personnel departure. Platforms with continuous monitoring capabilities and continuous risk monitoring provide real-time oversight of vendor risk, enabling organizations to spot vulnerabilities and changes as they happen. Risk intelligence feeds and risk intelligence deliver ongoing, dynamic insights that support proactive detection of cyber risk and emerging threats. Features such as risk thresholds and risk tracking allow organizations to define acceptable risk levels, monitor for breaches, and respond quickly to changes in vendor risk. Continuous monitoring of third-party risk enables organizations to detect emerging issues, breaches of risk thresholds, or declining vendor performance earlier, supporting faster escalation and more informed decision-making. Platforms that provide continuous monitoring of vendors’ external-facing security posture, alongside periodic structured assessments, maintain a more current view of risk than those relying entirely on questionnaire cycles.
Connection to the broader compliance programme
Vendor risk does not exist in isolation from the rest of the compliance programme. Framework mapping and integration with the risk management platform are essential for connecting vendor risk to the broader risk management program, ensuring that risks, controls, and mitigation actions are aligned with standards like ISO 27001, SOC 2, HIPAA, and PCI DSS. DORA’s requirements around ICT third-party obligations connect vendor risk to the ICT risk management framework, to incident reporting requirements, and to the operational resilience testing programme. Risk processes should be automated and visible across the compliance program to support regulatory compliance and compliance officers, enabling streamlined oversight and audit readiness. Selecting the right third-party risk management software depends on features and how well the platform aligns with your organization’s size, risk profile, and regulatory complexity. VRM platforms that integrate with the broader GRC system — so vendor risk findings feed into the risk register and control evidence — produce a more complete picture than standalone vendor risk tools.
Risk-based tiering
Not all vendors carry equal risk. A cloud provider hosting production systems is a different risk category from a stationery supplier. Effective risk-based tiering should consider both inherent risk—the level of risk present before controls are applied—and residual risk, which is the risk remaining after controls are implemented, when assigning assessment depth and monitoring frequency. Platforms that support risk-based tiering—assigning assessment depth and monitoring frequency based on the criticality, inherent and residual risk, and exposure of each vendor relationship—allow compliance teams to allocate effort proportionately rather than applying the same process to every supplier in the register. Risk thresholds can be defined within these systems to help organizations prioritize supplier risk, trigger alerts when risks exceed acceptable levels, and allocate resources effectively. Modern third-party risk management software consolidates risk assessments, inherent and residual risk scoring, control mapping, and remediation workflows into a single system of record, streamlining the management of supplier risk and supporting regulatory compliance.
The 8 Best Risk Management Software Vendors in 2026
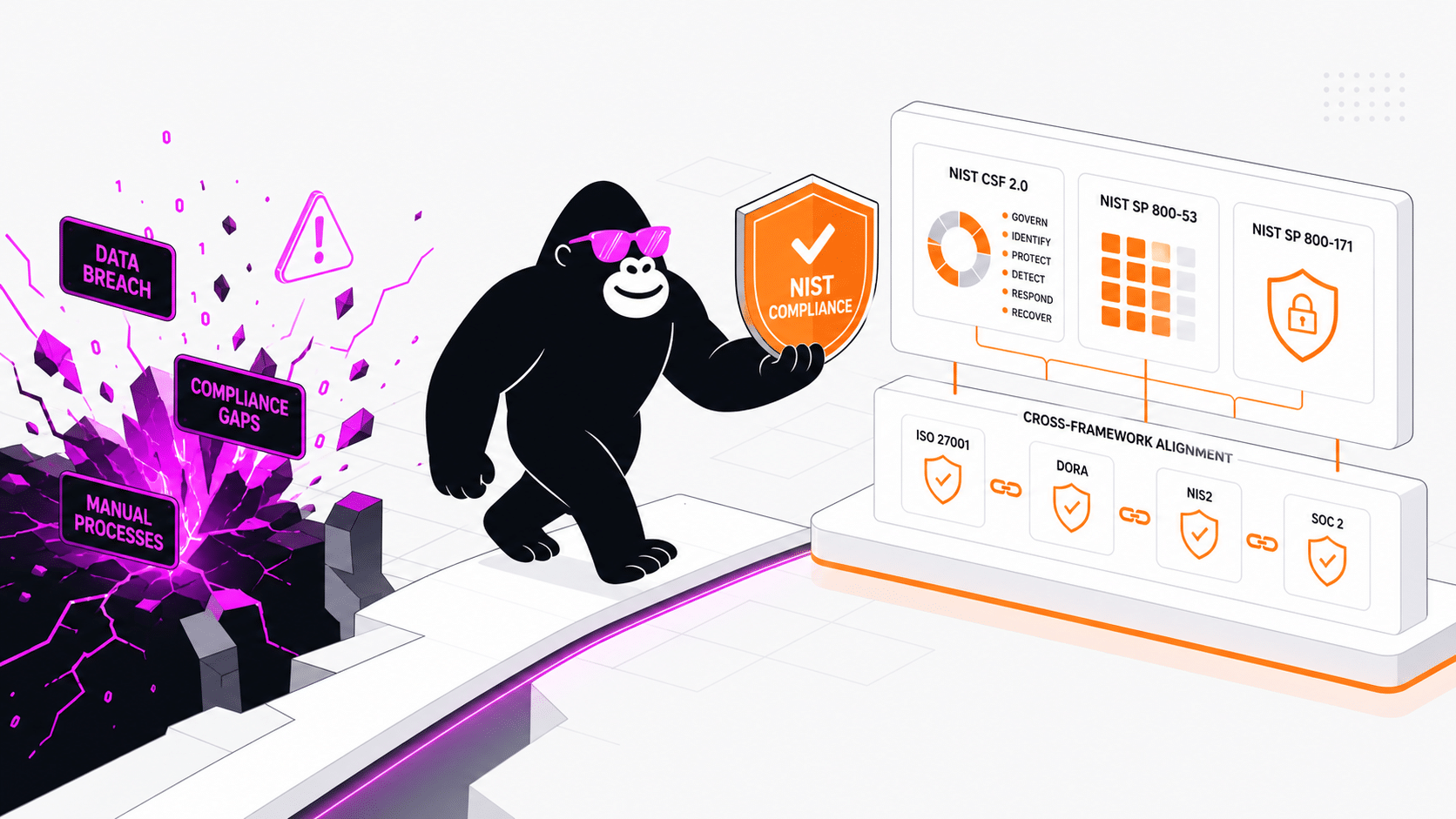
1. Copla — Best for EU Financial Institutions Under DORA
Copla’s vendor risk management capability sits within its connected compliance platform — which means vendor assessments connect directly to the ICT risk register, control evidence, and the documentation required by DORA’s supervisory expectations. The ICT third-party register is maintained within the platform rather than as a separate spreadsheet, and the risk assessment process follows DORA’s requirement for proportionate oversight based on the criticality of the ICT service.
For DORA-regulated entities, this integration is the material difference from standalone VRM tools. When a vendor relationship changes — a new contract, a significant service update, a reported incident — the downstream implications for the ICT risk register and control documentation surface in the platform rather than requiring manual updates across disconnected systems. The consultancy layer ensures the register format and assessment methodology satisfy supervisory expectations, not just internal governance requirements.
Copla supports approval workflows, audit trails, audit preparation, and automated reporting to streamline regulatory compliance. The platform automates evidence collection, risk tracking, and risk reporting, and supports framework mapping and risk thresholds to ensure continuous oversight and alignment with industry standards.
Best for: EU financial institutions managing DORA ICT third-party obligations and vendor risk within a connected compliance programme.
Frameworks: DORA, ISO 27001, NIS2, SOC 2, PCI DSS.
What sets it apart: DORA-specific ICT third-party register, integration with the broader risk and compliance programme, expert guidance on satisfying supervisory expectations, and robust support for approval workflows, audit trails, audit preparation, automated reporting, regulatory compliance, automated evidence collection, risk tracking, risk reporting, framework mapping, and risk thresholds.
Limitations: Focused on EU regulatory contexts. Less suited to US-centric third-party risk programmes.
Note: MetricStream is recognized for strong analytics and flexible workflows for enterprise-wide risk management, which may be relevant for organizations seeking advanced analytics capabilities.
2. Vanta — Best for Automated SaaS Vendor Risk Management
Vanta’s vendor risk management module combines AI-assisted questionnaire review with continuous security monitoring, reducing the manual effort of maintaining vendor risk programmes at scale. Its AI reads vendor documentation, flags risks, and generates remediation tickets — shifting the compliance team’s role from data collection to prioritisation and verification. For SaaS companies managing large vendor portfolios alongside their compliance programmes, the automation depth makes ongoing oversight manageable without growing the team proportionately.
Best for: SaaS companies managing vendor risk as part of their SOC 2 or ISO 27001 compliance programmes.
What sets it apart: Vanta automates evidence collection, risk tracking, and risk reporting, and supports automated reporting and approval workflows to streamline and standardize processes such as vendor onboarding, risk assessments, compliance checks, and issue resolution. The platform leverages risk intelligence and risk intelligence feeds for proactive risk management, providing real-time insights into emerging threats and vendor risks. Vanta also automates risk registers by linking them to continuous control testing and vendor monitoring, ensuring ongoing compliance and operational resilience. AI-assisted questionnaire automation, continuous monitoring, and integration with the broader compliance platform further distinguish Vanta.
Limitations: DORA-specific functionality is limited. The platform is designed for the SaaS market rather than EU financial services regulatory contexts.
3. OneTrust — Best for Privacy-Led Vendor Risk
OneTrust’s third-party risk module sits within its broader privacy and GRC platform, making it the natural choice for organisations whose vendor risk programme is led by GDPR data processing obligations rather than ICT security risk. Data processor agreements, data protection impact assessments for vendor relationships, and ongoing monitoring of third-party data handling practices are all supported with greater depth than security-first VRM platforms.
Best for: Organisations whose vendor risk is primarily governed by GDPR and data privacy obligations.
What sets it apart: OneTrust supports framework mapping, enabling automatic alignment of risks, controls, and mitigation actions with standards like ISO 27001, SOC 2, HIPAA, and PCI DSS. It streamlines vendor compliance processes and automates vendor security questionnaires and security questionnaires, making it easier to assess, track, and manage third-party risk. OneTrust’s focus on privacy, security, and third-party risk management makes it especially suitable for mapping data flows and vendor risks.
Limitations: Security and operational risk depth is limited relative to dedicated VRM or ICT risk platforms.
4. Panorays — Best for Continuous External Vendor Monitoring
Panorays combines continuous, non-intrusive external monitoring of vendors’ security posture with automated assessment workflows — so the view of a vendor’s risk is never more than the latest scan rather than the last completed questionnaire. Its approach is built on the recognition that annual reviews are fundamentally inadequate when a vendor’s security posture can change at any moment.
Best for: Organisations that need continuous visibility into vendor security posture alongside structured assessment workflows.
What sets it apart: Panorays offers continuous monitoring capabilities and continuous risk monitoring, integrating risk intelligence and risk intelligence feeds to provide real-time insights into cyber risk and supplier risk. This enables proactive detection of fluctuations in vendor risk exposure, control gaps, and concentration risk across the third-party ecosystem. Automated assessments and compliance mapping across multiple frameworks further enhance its ability to deliver greater data insights and operational resilience.
Limitations: Continuous monitoring provides an external view of vendor posture; it does not replace structured internal assessments for regulatory purposes.
5. Prevalent — Best for Comprehensive TPRM Lifecycle Management
Prevalent manages the full vendor risk lifecycle—including onboarding, due diligence, ongoing monitoring, remediation, and offboarding—within a single risk management platform. As a leading TPRM software, Prevalent supports the entire risk management program by automating risk processes and approval workflows, ensuring structured, transparent decision-making and accountability throughout vendor management. Its AI-powered risk assessments and continuous monitoring features streamline third-party risk management, while integration with procurement and legal workflows embeds risk assessment directly into the vendor onboarding process. Prevalent also helps organizations build and maintain a comprehensive vendor inventory, which is foundational for effective third-party risk assessment and ongoing oversight.
Best for: Organisations with large, complex vendor ecosystems that need structured lifecycle management from onboarding through offboarding.
What sets it apart: Full lifecycle VRM, comprehensive risk management platform capabilities, automation of risk processes and approval workflows, AI-assisted risk scoring, supply chain visibility extending to fourth-party dependencies, and robust vendor inventory management.
Limitations: Enterprise pricing and implementation complexity. Less suited to mid-market regulated businesses.
6. Hyperproof — Best for VRM Within Multi-Framework Compliance Programmes
Hyperproof’s vendor risk management integrates with its broader compliance workflow platform, connecting vendor assessments to the control evidence and risk registers that multi-framework compliance programmes require. For organisations managing vendor risk alongside SOC 2, ISO 27001, and other frameworks, the cross-framework evidence reuse reduces the duplication of work that standalone VRM tools create.
Best for: Mid-to-large organisations managing vendor risk as part of multi-framework compliance programmes.
What sets it apart: Hyperproof supports framework mapping, automates evidence collection, and provides automated reporting, risk reporting, and risk tracking. The platform maintains detailed audit trails and supports audit preparation, making it easier to meet standards such as ISO 27001, HIPAA, and GDPR. Modern risk management software like Hyperproof centralizes the risk lifecycle—from intake and scoring to treatment, exceptions, and reporting. Integration with compliance workflows, cross-framework evidence reuse, and task management across distributed teams further distinguish Hyperproof.
Limitations: VRM is not the primary focus of the platform — organisations with complex standalone VRM requirements may find the depth insufficient.
7. Drata — Best for Automated Vendor Risk in SaaS Compliance
Drata’s vendor risk management centralises assessments and puts the workflow on autopilot — automated questionnaires, real-time risk monitoring, and integration with the compliance programme mean vendor risk does not require a separate team to manage. Its pre-built risk library based on NIST SP 800-30 and ISO 27005 provides structured starting points for vendor risk assessment rather than requiring organisations to build methodology from scratch.
Best for: SaaS companies managing vendor risk within their existing Drata compliance programme.
What sets it apart: Drata automates evidence collection, risk tracking, and risk reporting, and supports automated reporting and approval workflows to streamline and standardize vendor onboarding, risk assessments, compliance checks, and issue resolution. Automated risk assessments involve automating evidence collection and risk scoring. The platform leverages risk intelligence and risk intelligence feeds for proactive risk management, providing dynamic insights and continuous monitoring to enhance operational resilience and compliance. Full automation of vendor assessment workflows, pre-built risk library, and integration with the broader compliance platform further distinguish Drata.
Limitations: DORA-specific third-party register requirements are not a primary design consideration.
8. SecurityScorecard — Best for External Vendor Security Ratings
SecurityScorecard provides continuous external security ratings for vendor portfolios — tracking organisations’ external-facing security posture through a standardised numerical score that enables rapid comparison across supply chains. It is not a VRM platform in the traditional sense (questionnaires, lifecycle management, regulatory documentation) but provides the external threat intelligence layer that most VRM programmes lack: visibility into whether your vendors’ security posture actually matches what their questionnaire responses indicate.
Best for: Organisations that want continuous external visibility into vendor security posture, cyber risk, and supplier risk alongside their structured VRM programme, and who require continuous monitoring capabilities and regulatory alignment.
What sets it apart: Empirical, continuous external ratings, continuous risk monitoring, advanced continuous monitoring capabilities, integration of risk intelligence and risk intelligence feeds for real-time updates on cyber threats and supplier risk, threat intelligence integration, and supply chain visibility.
Limitations: Ratings provide an external view — they do not manage the contractual, regulatory, or lifecycle dimensions of vendor risk.
Organizations searching for third-party risk management software should adopt platforms that support continuous monitoring and regulatory alignment.
Implementation and Integration
Successful implementation and integration of risk management software require a structured approach:
- Needs Assessment: Begin by identifying your organization’s specific risk management requirements, including regulatory obligations, risk categories, and existing workflows.
- Software Selection: Choose a risk management software solution that aligns with your needs, offering the necessary features for compliance management, risk assessment, and ongoing monitoring.
- Configuration and Data Migration: Configure the management software to match your risk management processes, upload relevant risk data, and establish user roles and permissions.
- User Training: Provide comprehensive training to ensure all stakeholders understand how to use the software effectively and follow risk management protocols.
- Integration: Connect the risk management software with existing systems, such as compliance management platforms, audit tools, and vendor management systems, to enable seamless data exchange and reduce manual effort.
A well-executed implementation and integration plan ensures that risk management software delivers maximum value, streamlines compliance management, and enhances the organization’s ability to manage risk proactively.
Risk Management Software Analytics
Analytics are a core component of modern risk management software, providing actionable insights that drive better risk management decisions:
- Risk Trends and Exposure: Analytics dashboards help organizations track risk trends over time, monitor risk exposure across different categories, and identify areas requiring immediate attention.
- Risk Controls and Performance: By analyzing the effectiveness of risk controls and vendor performance, organizations can optimize their risk management processes and allocate resources more efficiently.
- Advanced Analytics: Features such as predictive analytics and machine learning enable organizations to forecast emerging threats, identify potential vulnerabilities, and take proactive measures to mitigate risks.
- Informed Decision-Making: Risk management software analytics support compliance teams and decision-makers with real-time data, enabling informed decisions that reduce risk exposure and improve organizational resilience.
Leveraging analytics within risk management software empowers organizations to continuously improve their risk management processes and stay ahead of evolving risks.
How to Choose
For EU financial institutions, the starting question is DORA compliance. DORA’s ICT third-party risk requirements are prescriptive about what the register must contain, how risk assessments must be conducted, and what contractual arrangements must be in place. Platforms not designed for that regulatory context require significant customisation to meet supervisory expectations — customisation that creates ongoing maintenance burden and compliance risk.
Organizations should evaluate risk management platforms and risk management software based on their ability to support the risk management program, risk processes, and regulatory compliance. Features such as risk thresholds, risk reporting, risk tracking, framework mapping, approval workflows, audit trails, audit preparation, automate evidence collection, and automated reporting are critical for compliance officers managing multiple frameworks and ensuring audit readiness. Choosing the right risk management software should align capabilities with your operating model, risk appetite, and scale.
For organisations outside the EU regulatory context, the choice depends on whether vendor risk is primarily security-driven (in which case Vanta, Drata, or Prevalent are strong options), privacy-driven (OneTrust), or part of a broader enterprise risk programme (Optro, Hyperproof).
The DORA gap analysis is often the most effective starting point — it reveals which aspects of the third-party risk programme satisfy regulatory expectations and which require investment, before you commit to a platform designed for a different regulatory context.
Future of Risk Management Software
The future of risk management software will be defined by rapid technological advancements and evolving regulatory landscapes:
- Emerging Technologies: Artificial intelligence, blockchain, and the Internet of Things (IoT) are transforming risk management software, enabling real-time monitoring, automated risk assessment, and advanced analytics capabilities.
- Regulatory Adaptation: As industry standards and regulations such as GDPR and CCPA evolve, risk management software must adapt to ensure ongoing compliance and support for new requirements.
- Sophisticated Capabilities: Future management software will offer enhanced continuous monitoring, predictive analytics, and automated evidence collection, allowing organizations to identify risks and respond to emerging threats faster than ever.
- Growing Demand: As risk environments become more complex, organizations will increasingly rely on advanced risk management software to manage risk, maintain compliance, and achieve business objectives.
By investing in innovative risk management software and staying aligned with industry standards, organizations can strengthen their risk management programs and remain resilient in the face of emerging risks.
Vendor risk management has moved from a compliance checkbox to an operational requirement. The organisations that manage it well are those that have stopped treating it as a periodic documentation exercise and started treating it as a continuous programme — monitoring vendor posture, maintaining current documentation, and connecting third-party risk to the rest of the compliance programme rather than managing it in isolation. Vendor risk management helps safeguard sensitive data, ensure operational continuity, and meet the complex demands of regulatory compliance.
How Copla Supports Vendor Risk Management
We maintain the DORA ICT third-party register, conduct structured vendor risk assessments aligned to supervisory expectations, and connect vendor risk findings to the broader ICT risk management framework — all within the same platform that manages your ISO 27001 and NIS2 obligations. Copla supports approval workflows, audit trails, audit preparation, and automated reporting to streamline regulatory compliance. The platform automates evidence collection, risk tracking, and risk reporting, and supports framework mapping and risk thresholds to ensure continuous oversight and alignment with industry standards. Effective risk management software like Copla provides a centralized repository of third parties, helping organizations understand the risks they introduce across the business.
Schedule a call with Copla to walk through how this would look for your team.
FAQ
-
What is the difference between vendor risk management and third-party risk management? +
The terms are largely interchangeable in practice. Third-party risk management (TPRM) is the broader category, covering all external relationships including suppliers, partners, and service providers. Vendor risk management (VRM) typically refers specifically to contracted suppliers. Most platforms use the terms interchangeably. TPRM software supports vendor compliance, vendor inventory, and automates vendor security questionnaires and security questionnaires to streamline onboarding, risk assessments, and ongoing monitoring.
-
What does DORA require for ICT third-party risk? +
DORA requires EU financial institutions to maintain a comprehensive register of all ICT third-party service providers, conduct structured risk assessments before entering into and during ICT service contracts, implement contractual provisions covering data security, audit rights, and business continuity, and ensure exit strategies are in place for critical ICT services. Supplier risk, inherent risk, residual risk, risk thresholds, and risk scoring are all part of the risk assessment process required to meet DORA’s standards. Supervisory authorities can examine this register and the supporting documentation during inspections.
-
How often should vendor risk assessments be conducted? +
At minimum, annually for critical or high-risk vendors, and upon significant contract changes, service changes, or reported incidents. Continuous external monitoring provides an ongoing view between formal assessment cycles. DORA’s proportionality principle allows assessment frequency to be calibrated based on the criticality and risk profile of each ICT service relationship. Modern risk management platforms and risk management software support risk tracking, risk reporting, audit trails, audit preparation, automate evidence collection, automated reporting, approval workflows, and framework mapping to ensure compliance and streamline the risk management program for compliance officers and risk processes.