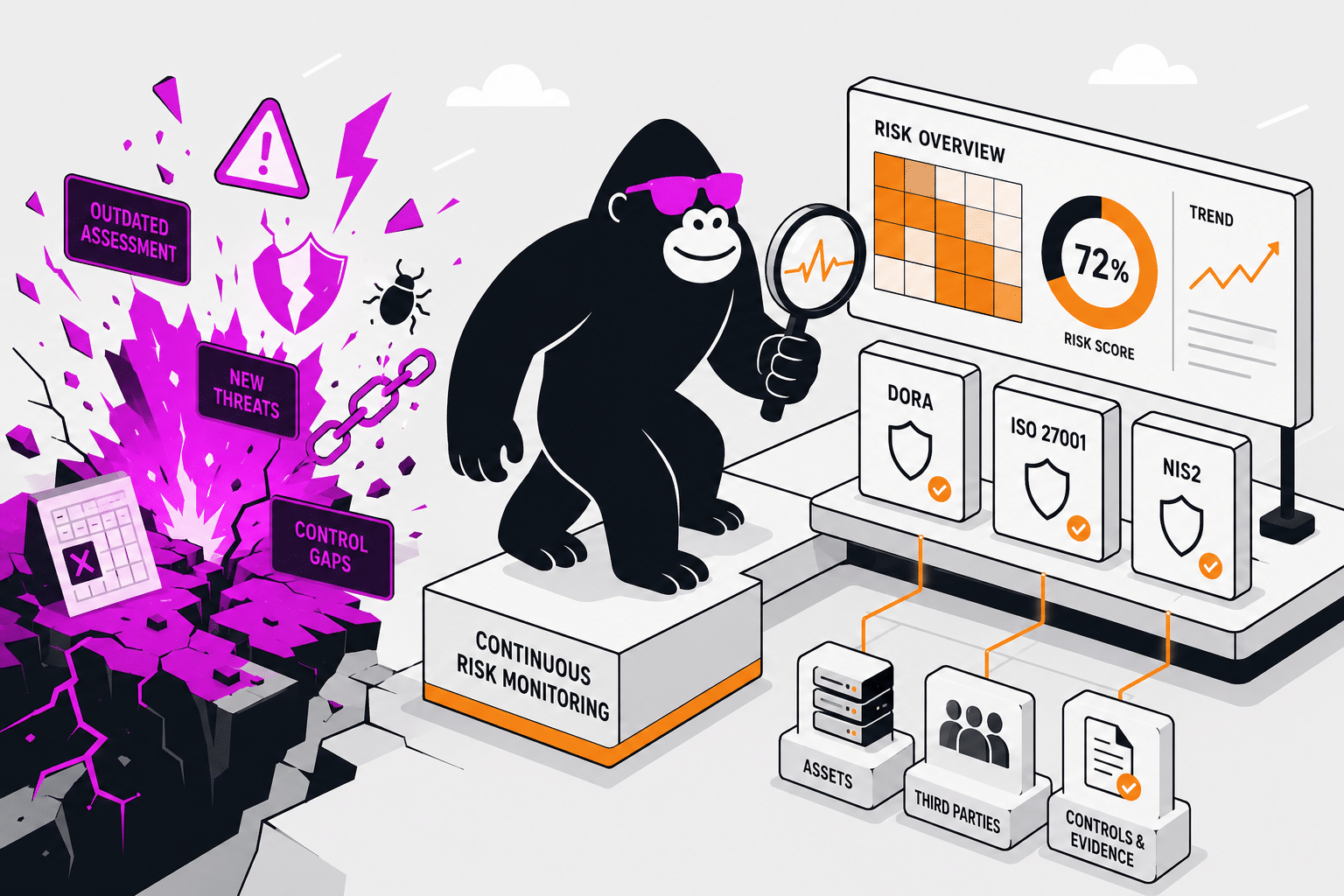
Most organisations do not have a risk management problem. They have a risk monitoring problem. The risks are documented — somewhere in a spreadsheet, a policy document, or an annual assessment that was accurate at the time it was completed. What organisations lack is a system that keeps those risks current as the business changes, flags emerging potential risks before they become incidents, and connects risk status to the risk controls and evidence that demonstrate the risks are being managed and mitigated. Risk controls are essential for managing and mitigating potential risks across various compliance areas.
This guide compares eight of the best risk monitoring software platforms in 2026, with particular attention to what continuous, connected risk monitoring looks like for EU financial institutions managing DORA, ISO 27001, and NIS2 obligations simultaneously. Effective risk monitoring software transforms risk management from a reactive manual process into a proactive, data-driven strategy, supporting effective risk management.
Risk monitoring software for SMEs focuses on ease of use, affordability, and often features AI-powered automation and intuitive dashboards.
What Is Risk Monitoring Software?
Risk monitoring software is a platform that maintains ongoing visibility into an organisation’s risk posture — tracking identified risks as they evolve, alerting teams when risk levels change, connecting risk status to the controls designed to address each risk, and producing the reporting that compliance programmes, boards, and regulatory supervisors require. The defining feature is continuity: risk monitoring is not a periodic activity but an ongoing one, reflecting operational reality in real time rather than at scheduled review intervals. By leveraging real-time risk data, risk monitoring software supports risk identification and risk analysis, enabling organisations to detect, assess, and respond to emerging threats more effectively.
The distinction between a risk register tool and risk monitoring software matters in practice. A risk register documents risks at a point in time. Risk monitoring software maintains a live view of those risks — updating automatically when the underlying environment changes, connecting risk status to control performance, and surfacing the signals that indicate a risk profile has changed before the next formal review cycle arrives. Automated workflows streamline repetitive tasks such as evidence collection and risk assessments, sending alerts for potential threats, changing risks, or expired controls, while real-time dashboards provide instantaneous visual representation of risk data, including heatmaps to highlight high-risk areas for rapid decision-making.
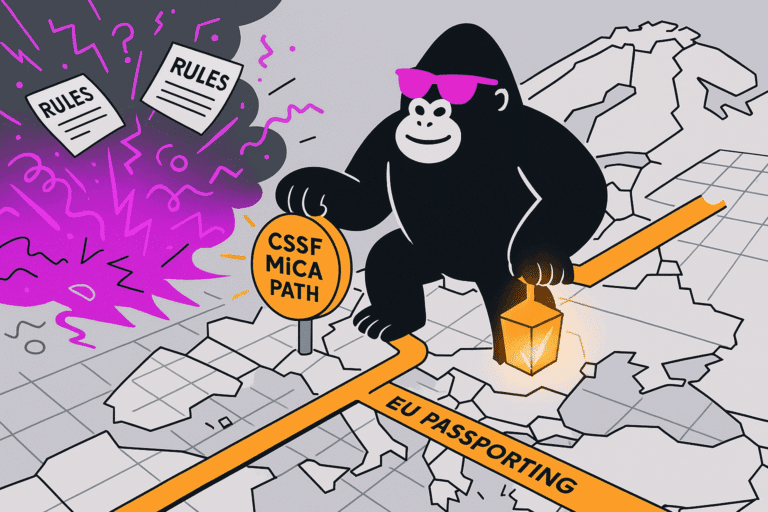
For EU financial institutions, the regulatory context has made this distinction concrete. DORA’s ICT risk management requirements assume ongoing risk monitoring as a continuous operational function — not a document produced annually and reviewed before supervisory examinations. ISO 27001:2022 similarly requires that risk assessments remain current as the organisation and its threat environment evolve. The platform that manages this function needs to reflect operational reality continuously, not periodically.
The Shift from Periodic to Continuous Risk Monitoring
The annual risk assessment is a relic of an era when risk environments changed slowly and documentation was the primary output of risk management. In 2026, the risk environment for regulated businesses changes continuously: new cloud services are provisioned, new third-party relationships are established, new threat intelligence emerges, and regulatory requirements evolve. A risk assessment completed twelve months ago may not reflect the organisation’s current exposure in any meaningful way. Real-time monitoring is essential to detect when new risks emerge, enabling organizations to respond swiftly to evolving threats as they arise.
Continuous risk monitoring addresses this by connecting the risk register to the operational environment it is supposed to reflect. When a new ICT service provider is onboarded, the risk register updates. When a control fails — an access review overdue, a vulnerability unpatched, a configuration changed — the affected risks surface immediately. When a vendor’s security posture deteriorates, the associated third-party risks update automatically rather than waiting for the next annual review. Effective TPRM platforms provide continuous monitoring of third-party risks, filling gaps between periodic assessments and allowing organizations to track new and evolving risks associated with third parties.
For EU financial institutions, this shift is not optional. DORA’s ICT risk management framework requires continuous monitoring of ICT risks and their controls as part of operational resilience. Supervisory authorities examining DORA compliance will look for evidence of ongoing risk monitoring — not just a risk assessment document. The platform you choose needs to produce that evidence continuously, not on demand.
What to Look For in Risk Monitoring Software
Live connection between risks, controls, and assets
The most important architectural question is whether the platform connects risks to the controls that address them and the assets that generate them, or manages all three as separate modules. In a connected architecture, a control failure surfaces in the risk register automatically — the risk level updates when the control operating it deteriorates. Effective risk monitoring software should also ensure robust compliance controls and maintain high risk scoring accuracy, providing reliable and up-to-date third-party risk assessments that support regulatory confidence and audit readiness. A centralized risk registry acts as a single source of truth, storing all risk-related data, control libraries, and incident reports to maintain a unified overview. Compliance and regulatory mapping often includes built-in frameworks for standards like ISO 27001 and GDPR, automating compliance tracking and streamlining alignment with industry regulations. A platform where risks and controls exist in separate systems requires manual reconciliation that nobody actually does between audit cycles, producing a risk register that increasingly diverges from operational reality.
Automated risk signals from the operational environment
Risk monitoring software that relies on users to manually update risk status is not monitoring — it is documentation maintenance. Platforms that pull signals from the operational environment automatically — cloud configuration states, access control logs, third-party security ratings, vulnerability scan results — maintain a live risk picture without requiring the compliance team to act as data entry operators. Many solutions also integrate threat intelligence feeds, providing continuous threat data from sources such as dark web forums and credential leak sources to better identify and mitigate potential security breaches. The effectiveness of these platforms depends on high-quality data, which is essential for accurate risk assessment, incident reporting, and informed decision-making. Additionally, many TPRM solutions utilize AI and machine learning to enhance risk analysis and monitoring capabilities, further improving the accuracy and efficiency of risk management.
Cross-framework risk mapping
For EU financial institutions managing risk across DORA, ISO 27001, and NIS2, risks need to be assessed once and mapped across all applicable frameworks simultaneously. A risk in the ICT risk register that relates to a cloud service provider is simultaneously a DORA third-party risk, an ISO 27001 supplier risk, and potentially an NIS2 relevant risk. Platforms that maintain separate risk registers for each framework produce duplication and inconsistency. Platforms that map risks across frameworks from a single register produce consistency and reduce overhead. Effective compliance tracking and a clear understanding of risk exposure across multiple frameworks are essential for comprehensive risk management, ensuring organizations can monitor regulatory adherence and identify vulnerabilities holistically.
Regulatory-grade risk documentation
The output of risk monitoring is not just internal dashboards — it is the documentation that regulatory supervisors examine. For DORA, that means ICT risk documentation in formats that supervisory authorities expect. For ISO 27001, it means risk assessment methodology, treatment decisions, and the Statement of Applicability connected to the underlying risk register. Automated reporting and analytics support audit readiness and executive reporting by enhancing the accuracy of risk assessment, streamlining compliance workflows, and helping organizations detect risks early while keeping stakeholders informed through comprehensive reporting tools. Platforms designed for generic enterprise risk management may produce useful internal reporting without producing documentation that satisfies regulatory examination standards.
Expert interpretation alongside tooling
Risk monitoring tools surface signals; they do not interpret their regulatory significance. A configuration drift alert from a cloud tool means something different in the context of a DORA ICT risk assessment than in the context of an internal security review. For regulated businesses without large in-house risk and compliance teams, access to expert guidance that translates monitoring outputs into regulatory implications is what determines whether the risk monitoring function actually reduces compliance exposure or just produces better-organised documentation. By understanding organizational pain points and leveraging risk monitoring software to gain insights, organizations can improve decision-making through clear, actionable data and risk insights that align risk management with strategic business objectives.
The 8 Best Risk Monitoring Software Platforms in 2026
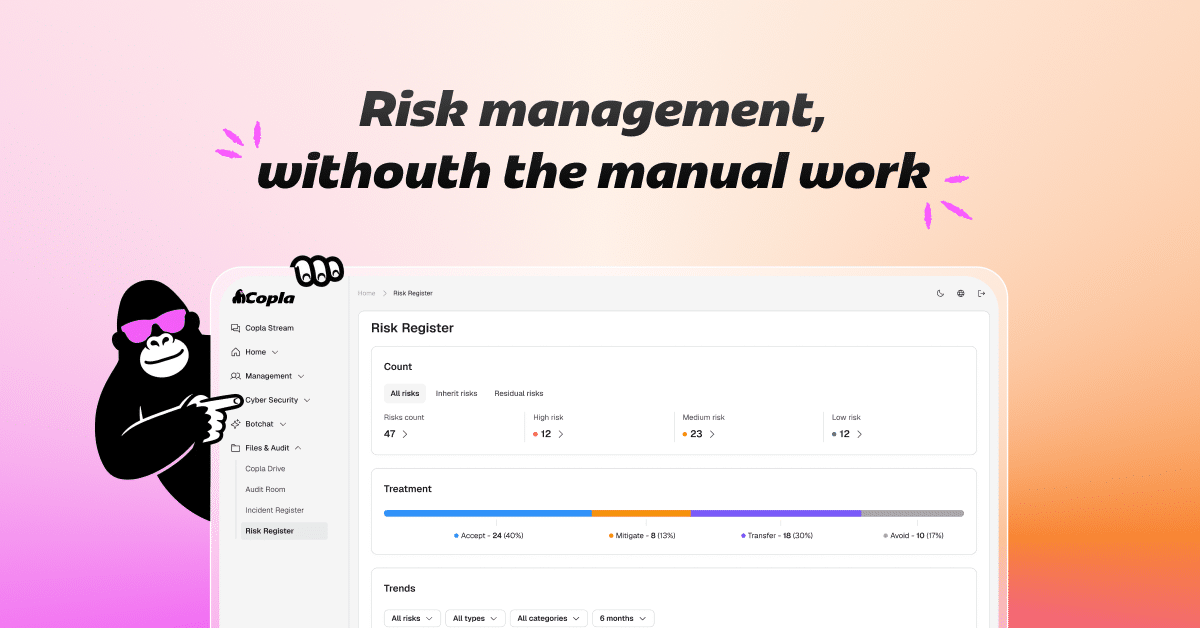
1. Copla — Best for Continuous Regulatory Risk Monitoring
Copla is built around the principle that risk monitoring should be continuous and connected — not a periodic assessment stored in a separate system from the controls it informs. The architecture starts from assets: the systems, data flows, and third-party suppliers that constitute the organisation’s ICT environment. Risks are generated from those assets and updated as the asset register changes. Controls are connected to the risks they address and monitored continuously — when a control fails, the affected risks update automatically. Documentation stays aligned with operational reality rather than reflecting a historical snapshot.
For DORA-regulated entities, this architecture directly satisfies the regulation’s continuous monitoring requirements. The ICT risk register is not a document produced for supervisory examination — it is the live operational record of the organisation’s risk posture, maintained in the platform and available on demand. The DORA gap analysis is built into the onboarding process, which means the risk monitoring programme starts from a clear picture of current posture rather than from a generic template.
The CISO consultancy layer addresses the interpretation gap that risk monitoring tools leave. When monitoring surfaces a signal — a new third-party risk, a control gap, a change in the threat environment — an expert interprets its regulatory significance and determines the appropriate response, rather than leaving that judgment to an internal team that may not have the regulatory context to make it. Risk committees, composed of representatives from multiple departments, can be involved in reviewing monitoring outputs and collaborating to prioritize remediation efforts, ensuring that remediation tasks are aligned with organizational priorities and improving overall security posture.
For ISO 27001 programmes, the risk monitoring function maintains the currency of the risk assessment that the ISMS requires — so the risk register presented to Stage 2 auditors reflects the current state of the business, not the state it was in when the assessment was last formally completed.
Best for: EU financial institutions, fintechs, payment institutions, and regulated SMEs needing continuous risk monitoring across DORA, ISO 27001, and NIS2 from a single connected system.
Frameworks: ISO 27001, DORA, NIS2, SOC 2, PCI DSS, Cyber Essentials.
What sets it apart: Asset-driven continuous risk monitoring, live connection between risks and controls, cross-framework risk mapping, and expert interpretation built into the engagement rather than sold separately.
Limitations: Optimised for EU regulatory contexts. Less suited to US-only risk programmes (HIPAA, FedRAMP) or operational project risk management.
2. Vanta — Best for Continuous Compliance Risk Monitoring in SaaS
Vanta’s continuous monitoring connects to cloud infrastructure, identity systems, and developer tooling to track control status in real time — surfacing risks when controls fail or configurations drift before the next audit cycle. Its risk management module connects identified risks to the controls designed to address them, with automated tests monitoring control effectiveness continuously rather than periodically. For SaaS companies managing compliance risk as a live programme rather than an annual exercise, Vanta’s monitoring depth and integration breadth make it the default starting point.
Best for: SaaS companies and fintechs managing compliance risk continuously across SOC 2, ISO 27001, and GDPR.
Frameworks: SOC 2, ISO 27001, HIPAA, GDPR, PCI DSS, DORA (recently added).
What sets it apart: Integration breadth across 300+ cloud tools, continuous control monitoring, and real-time risk dashboard. Vanta’s API integrations enable seamless data sharing and integration with third party services, enhancing TPRM process automation, compliance workflows, and overall data flow and risk visibility across the organization.
Limitations: Risk management is a feature of the compliance platform rather than the foundation of it. DORA and NIS2 regulatory risk monitoring depth is limited compared to EU-specific platforms.
3. Optro (formerly AuditBoard) — Best for Enterprise Risk Monitoring and Audit Integration
Optro’s connected risk architecture links enterprise risk, compliance, and internal audit in a single platform — so risk monitoring signals feed directly into the audit programme rather than existing in a separate system. Continuous monitoring with key risk indicators detects control failures between assessments, and AI-powered issue management assigns and suggests remediation actions automatically. For large financial institutions where risk monitoring is a board-level function informing strategic decisions as well as operational compliance, Optro’s enterprise depth is relevant.
Best for: Large financial institutions and enterprises running integrated risk monitoring, audit, and compliance programmes at scale.
Frameworks: 40+, including DORA, ISO 27001, SOC 2, ISO 42001, NIST CSF, PCI DSS, HIPAA.
What sets it apart: Continuous monitoring with KRI alerts, enterprise risk aggregation, AI-assisted issue management, integration with internal audit workflows, and automated workflows supporting vendor onboarding and vendor due diligence. Optro automates vendor risk assessments, streamlining the onboarding process, improving efficiency, and reducing manual errors in evaluating and monitoring vendor security posture.
Limitations: Implementation complexity and cost make it over-engineered for mid-market regulated businesses. Mid-market regulated businesses will find the operational overhead disproportionate.
4. Drata — Best for Real-Time Compliance Risk Monitoring
Drata monitors compliance risks continuously — control failures surface in real time rather than at the next scheduled check, and the risk posture dashboard reflects live status across all monitored frameworks. Its pre-built risk library maps to NIST SP 800-30 and ISO 27005, providing structured starting points that connect risk assessments to the compliance programme rather than requiring a separate risk methodology. Cross-framework risk mapping reduces duplicate assessments for organisations managing SOC 2, ISO 27001, and GDPR simultaneously.
Best for: Fast-growing companies that need real-time visibility into compliance risk posture across multiple frameworks.
Frameworks: SOC 2, ISO 27001, HIPAA, GDPR, PCI DSS.
What sets it apart: Real-time control monitoring feeds the risk dashboard live, pre-built risk library mapped to industry standards, cross-framework deduplication, and the use of completed security questionnaires to identify compliance gaps and streamline risk assessments.
Limitations: Governance and regulatory risk depth (DORA, NIS2 supervisory context) is limited. Risk management is secondary to the compliance automation core.
5. MetricStream — Best for Enterprise Cyber and Operational Risk Monitoring
MetricStream integrates cyber, IT, operational, and third-party risk monitoring into a single platform — with predictive analytics, heat maps, and AI-driven insights that identify emerging risks and prioritise mitigation before issues escalate. Its regulatory change management capability monitors evolving regulatory requirements across jurisdictions and maps their impact to the organisation’s control environment, reducing the lag between a regulatory change and the compliance programme’s response. For global enterprises managing risk monitoring across multiple business lines and regulatory jurisdictions simultaneously, MetricStream’s depth is unmatched.
Best for: Large multinationals and financial institutions managing enterprise-wide risk monitoring across cyber, operational, third-party, and regulatory risk domains.
Frameworks: Broad enterprise coverage across financial services, cybersecurity, ESG, and operational risk frameworks.
What sets it apart: Advanced third party risk management features, including comprehensive third party risk assessments, continuous vendor risk monitoring, and real-time tracking of external threats and emerging threats. MetricStream supports continuous monitoring in TPRM, enabling organizations to track new and evolving risks associated with third parties. Its platform can assess up to 16 distinct third-party risks, providing deep visibility and integration within enterprise risk management. Predictive risk analytics, regulatory change management AI, and enterprise-wide risk aggregation further set it apart.
Limitations: Implementation timelines and professional services costs are substantial. Not suited to mid-market organisations without dedicated risk management functions.
6. Hyperproof — Best for Risk Monitoring in Multi-Framework Compliance Programmes
Hyperproof’s risk register connects to its compliance workflow platform — risks link to controls, controls link to evidence, and the entire programme is maintained from a single workspace. Its real-time dashboards provide visibility into risk posture and compliance status simultaneously, with the ability to filter by framework, control owner, or risk category to surface the specific information relevant to each stakeholder. For compliance teams managing risk monitoring across five or more concurrent frameworks with distributed ownership, Hyperproof’s coordination features maintain programme coherence without relying on email and spreadsheet management.
Best for: Mid-to-large organisations maintaining risk monitoring across multiple concurrent compliance frameworks with distributed control ownership.
Frameworks: SOC 2, ISO 27001, NIST CSF, HIPAA, PCI DSS, GDPR, and custom frameworks.
What sets it apart: Extensive library of configurable risk controls, proactive risk mitigation efforts, and tools that allow businesses to identify, assess, and respond to threats in real time by centralizing information and automating repetitive tasks. Also features risk-to-control-to-evidence linkage, cross-framework risk mapping, and real-time dashboard visibility.
Limitations: Continuous monitoring automation is less deep than Vanta or Drata. Less suited to organisations building risk monitoring from scratch without existing programme maturity.
7. Resolver — Best for Corporate Security and Operational Risk Monitoring
Resolver focuses on corporate security and operational risk monitoring — identifying risks, creating audit reports, standardising and automating risk management processes, and continuously assessing risks through AI-driven insights. Its incident management workflows connect risk monitoring to the response and remediation functions that turn identified risks into managed outcomes. Resolver centralizes incident and risk tracking in a single cloud-based hub, unifying risk data for improved assessment accuracy and reporting. For organisations where operational security risks — physical security, investigations, incident response — are as significant as regulatory compliance risks, Resolver’s operational depth is relevant.
Best for: Organisations managing operational and corporate security risk monitoring alongside compliance risk.
Frameworks: Enterprise risk management, ISO 31000, and compliance frameworks.
What sets it apart: Streamlined risk management processes, centralized and actionable risk data, straightforward design and quick setup, operational security risk depth, incident management integration, and AI-assisted risk assessment.
Limitations: Regulatory compliance framework depth (ISO 27001, DORA, NIST) is less developed than dedicated compliance platforms.
8. LogicGate Risk Cloud — Best for Configurable Third Party Risk Management Workflows
LogicGate’s no-code platform allows organisations to build custom risk monitoring workflows around their specific governance model and risk taxonomy. For organisations with established risk frameworks that do not map neatly to the pre-built structures of compliance-first platforms, the ability to configure monitoring workflows, escalation paths, and risk scoring models without developer involvement is a meaningful advantage. Its real-time risk quantification capabilities translate risk exposures into financial impact terms, supporting more informed resource allocation and making risk monitoring outputs more actionable for executive and board reporting.
Best for: Organisations with established risk methodologies that need configurable monitoring workflows and financial risk quantification.
Frameworks: Configurable — SOC 2, ISO 27001, NIST, custom frameworks.
What sets it apart: No-code configurability, financial risk quantification, flexible workflow design, and actionable insights for resource allocation and risk exposure.
Limitations: Configuration investment required upfront. Less suited to organisations that want a guided, pre-built risk monitoring programme.
How to Choose the Right Risk Monitoring Platform
The most useful framing is not “which platform has the best risk monitoring features” but “what does my organisation actually need to monitor, and what happens when the monitoring surfaces a finding.” When evaluating risk monitoring software, organizations should also conduct a cost benefit analysis to justify the investment, weighing the costs against the tangible and intangible benefits the platform provides.
For EU financial institutions, the answer to the second question has regulatory dimensions that generic risk monitoring tools do not address. When DORA’s ICT risk monitoring surfaces a new third-party vulnerability, the required response involves DORA supply chain risk management considerations — contract review, risk reassessment, potentially supervisory notification — that a dashboard alert does not manage. The platform needs to connect monitoring to the regulatory response workflows that those signals trigger.
For SaaS companies managing compliance risk, the question is whether risk monitoring is a standalone function or integrated with the compliance programme. Platforms that maintain separate risk monitoring and compliance management systems create the same fragmentation they are supposed to solve — just with better-organised fragmentation. Platforms that connect risk monitoring to control evidence, audit workflows, and compliance reporting produce a single operational picture. Operational efficiency and ongoing support are also important considerations; automating manual tasks within the platform can improve cost and time efficiency by lowering administrative costs and reducing the time required to detect and address risks.
The scale question matters too. Enterprise risk monitoring platforms — MetricStream, Optro, ServiceNow — are designed for large organisations with dedicated risk functions, multi-year implementation budgets, and complex governance structures. For mid-market regulated businesses, the complexity and cost of those platforms typically exceeds the value they deliver. The right platform for a 100-person fintech is not a scaled-down version of what a global bank needs — it is a platform designed for the mid-market context from the ground up.
Frequently Asked Questions
What is the difference between risk monitoring and risk management?
Risk management is the full lifecycle: identifying risks, assessing their likelihood and impact, selecting treatment options, implementing controls, and monitoring outcomes. Risk monitoring is the continuous function within that lifecycle — tracking risk status as it evolves, detecting when risk levels change, and alerting the relevant owners before identified risks materialise into incidents. Risk monitoring software supports the monitoring function specifically; risk management software may cover the full lifecycle including assessment, treatment planning, and reporting. Organizations use risk monitoring software to manage risk and mitigate risks as part of a continuous, iterative process that adapts to changing markets, technologies, and threats.
How does continuous risk monitoring differ from annual risk assessments?
Annual risk assessments produce a risk register that reflects the organisation’s risk posture at a point in time. Continuous risk monitoring maintains that picture dynamically — updating automatically when the underlying environment changes, connecting risk status to control performance in real time, and surfacing new risks as they emerge rather than waiting for the next scheduled review. For regulatory purposes, continuous monitoring is increasingly what supervisory authorities expect to see: not just a document, but evidence of an ongoing risk management function.
What does DORA require for risk monitoring?
DORA’s ICT risk management framework requires EU financial institutions to maintain a continuous ICT risk monitoring function — identifying and classifying ICT risks, implementing controls proportionate to those risks, and monitoring control effectiveness on an ongoing basis. The ICT risk register must be maintained continuously and made available to supervisory authorities on request. DORA’s operational resilience testing requirements also assume that ICT risks are monitored continuously rather than assessed periodically, so that testing programmes address current risk exposures rather than historical ones.
How does risk monitoring software connect to compliance programmes?
The most effective risk monitoring software connects directly to the compliance programme rather than existing alongside it. Risks connect to the controls designed to address them; control failures update risk status automatically; risk monitoring outputs feed into audit evidence packages and regulatory documentation. Platforms where risk monitoring and compliance management are separate functions — even if both are nominally supported — produce documentation that diverges from operational reality as quickly as manual approaches do. The connection between monitoring signals and compliance evidence is what distinguishes operational risk monitoring from better-organised documentation.
The risk monitoring function is where compliance programmes prove they are operational rather than documentary. Any organisation can produce a risk assessment document. The organisations that manage regulatory risk effectively are those that maintain a live connection between their documented risks and the operational environment those risks describe — so that when something changes, the compliance programme reflects it immediately rather than at the next scheduled review. In 2026, for EU financial institutions managing DORA, ISO 27001, and NIS2 simultaneously, that continuous connection is not a best practice — it is what the regulatory frameworks require. Enterprise Risk Management (ERM) is a systematic approach that enables organizations to identify, assess, manage, and monitor risks across all departments and functions.
How Copla Supports Continuous Risk Monitoring
We build risk monitoring programmes that reflect operational reality continuously — connecting asset registers, risk registers, and control evidence into a live system that updates as the business changes. This approach enables effective risk mitigation by providing a comprehensive view of your risk landscape, including third-party cyber risks, asset reputation, credential compromises, and dark web monitoring. By integrating these elements, organizations strengthen business continuity and operational resilience, ensuring they are better prepared for and can recover more quickly from unexpected disruptions, thereby safeguarding long-term sustainability. For EU financial institutions, the programme satisfies DORA’s continuous ICT risk monitoring requirements and ISO 27001’s ongoing risk assessment obligations from a single connected system, with expert CISO consultancy interpreting monitoring outputs in the regulatory context they belong to.
Schedule a call with Copla to walk through how this would look for your team.