SOC 2 has become the baseline trust signal for B2B software companies. Enterprise procurement teams ask for it. Security questionnaires reference it. Sales cycles stall without it. The complexity of managing SOC 2 compliance has increased significantly, with many reports now containing over 150 security controls—driving the need for more sophisticated software solutions. As organizations embark on their compliance journey, they seek platforms that support them every step of the way, addressing unique compliance needs and offering strong integration capabilities to reduce manual work and streamline the entire process. But the compliance software market that has grown up around SOC 2 ranges from excellent to superficial, and the difference matters more than most first-time evaluators appreciate. This guide compares eight of the best SOC 2 compliance software platforms in 2026, with honest assessments of what each does well and where each falls short.
What Is SOC 2 Compliance Software?
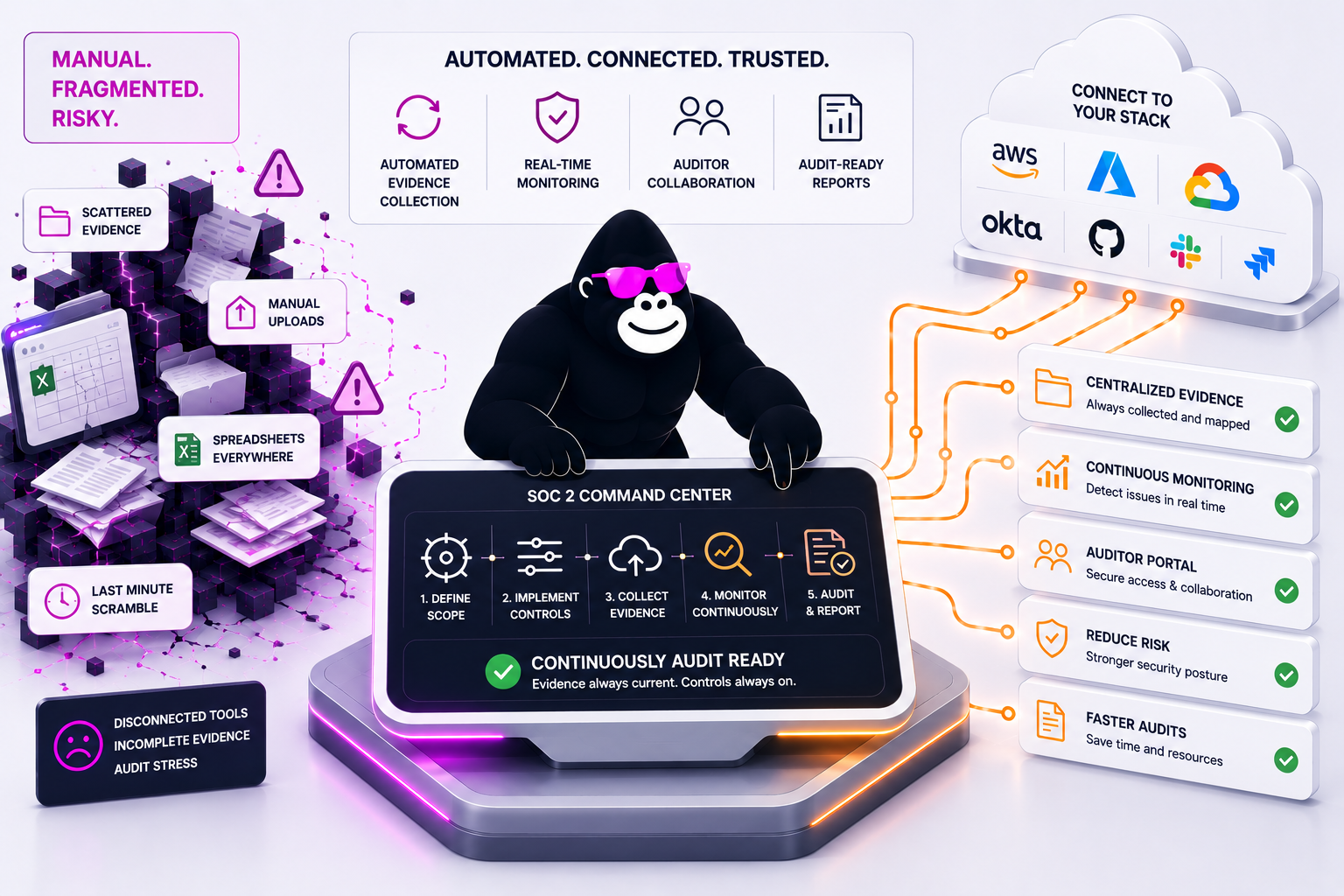
SOC 2 compliance management software supports the entire compliance process, including risk management, policy development, audit preparation, and ongoing monitoring. These platforms streamline the audit process by automating audit evidence collection and documentation, significantly reducing the need for manual evidence collection. By connecting to your cloud infrastructure, identity systems, and development tools, SOC 2 compliance software continuously collects audit evidence, mapping it to SOC 2 Trust Services Criteria, and managing the audit workflow that culminates in a Type I or Type II report. The best compliance management software replaces the manual scramble of gathering screenshots and updating spreadsheets before each audit with a system that maintains audit readiness as a continuous operational state, simplifying compliance management and supporting security compliance.
Compliance data is continuously gathered and mapped to the trust service criteria, supporting security compliance and simplifying compliance management. This automation not only streamlines tedious manual tasks but also prepares you for audits more efficiently by tracking your security controls and collecting evidence for audits.
The difference between a SOC 2 Type I (controls exist as of a point in time) and Type II (controls operated effectively over a period — typically 6–12 months) matters for platform selection. Type I is a documentation exercise that most platforms handle adequately. Type II requires demonstrating ongoing effectiveness over a monitoring period — which requires continuous, automated evidence collection, not periodic snapshots. Compliance workflows are automated, reducing manual work and ensuring that audit-ready reports are generated automatically, further simplifying the audit process and enhancing overall security compliance.
Accelerate SOC 2 certification
Losing clients due to a prolonged SOC 2 certification process
is a risk your business simply can’t afford.
Benefits of SOC 2 Compliance Software
SOC 2 compliance software delivers significant advantages for organizations seeking to streamline compliance management and strengthen their security posture. By automating key compliance tasks, these platforms help reduce manual effort and ensure ongoing audit readiness. Key benefits include:
- Improved audit readiness: SOC 2 compliance software maintains a continuous state of audit preparation, reducing the stress and uncertainty of manual audit cycles.
- Increased efficiency: Automated workflows and evidence collection minimize manual effort, freeing up resources for core business activities and reducing audit time.
- Enhanced security posture: Continuous monitoring and risk management features help organizations identify and address security gaps, protecting sensitive customer data and reducing the risk of data breaches.
- Simplified compliance management: A centralized compliance platform makes it easier to track compliance status, manage evidence collection, and maintain compliance with SOC 2 and other industry standards.
- Reduced risk of non-compliance: Automated evidence collection and real-time monitoring help organizations maintain compliance and quickly address any compliance gaps.
By leveraging SOC 2 compliance software, organizations can more effectively manage compliance requirements, protect customer data, and demonstrate trust to clients and partners.
What to Look For
Evidence automation depth
The value of SOC 2 software is measured by how much audit evidence and compliance data it collects automatically versus how much requires manual evidence collection or manual upload. Deep integration capabilities with your existing systems, tech stack, and tools—such as Okta, Jira, and Coupa—are essential for automating the collection and documentation of audit evidence and compliance data. Platforms with shallow integration coverage automate the easy parts (policy acknowledgements, employee training records) and leave the hard parts (access review evidence, configuration states, penetration test results) to manual collection. In contrast, platforms with strong integration capabilities across your actual tech stack—not just the popular ones—ensure that evidence flows automatically from your existing tools into the compliance platform, reducing manual effort and streamlining compliance workflows. Seamless integration with existing tools is key to reducing manual evidence collection and supporting efficient, audit-ready SOC 2 compliance.
Auditor access and workflow
The auditor experience matters more than most evaluators appreciate at the start. Platforms with streamlined compliance workflows and automated reporting features simplify the audit process for both organizations and auditors, ensuring documentation is always up to date. Audit-readiness features help organize and present audit evidence in an orderly fashion, making the audit process more efficient and less stressful. A platform that your auditor is familiar with reduces the back-and-forth of audit preparation significantly. A platform that requires extensive manual evidence export before the auditor can review anything adds weeks to the process. Ask which auditors work natively with the platform before signing.
Type II monitoring period support
Type II requires demonstrating control effectiveness over time. Continuous control monitoring and compliance monitoring provide real-time visibility into compliance status, helping organizations maintain audit readiness year-round. Platforms that monitor controls continuously — flagging failures in real time rather than at periodic checks — enable organizations to detect and address compliance gaps proactively and maintain a clean monitoring period record. Real-time monitoring of security controls is crucial for identifying potential security issues quickly and supporting swift response and recovery. Platforms that rely on periodic check-ins produce evidence that has gaps between checks, which auditors will notice.
Pricing transparency
SOC 2 software pricing varies enormously and is rarely published upfront. Budget for $8,000–$35,000 per year depending on team size and framework scope, and ask specifically about what is included versus billed separately (auditor access, additional frameworks, expert support). Organizations should ensure that pricing aligns with their specific compliance needs and the size or structure of their compliance teams.
The 8 Best SOC 2 Compliance Software Platforms in 2026
1. Copla — Best for Organisations That Need SOC 2 Alongside ISO 27001 or DORA
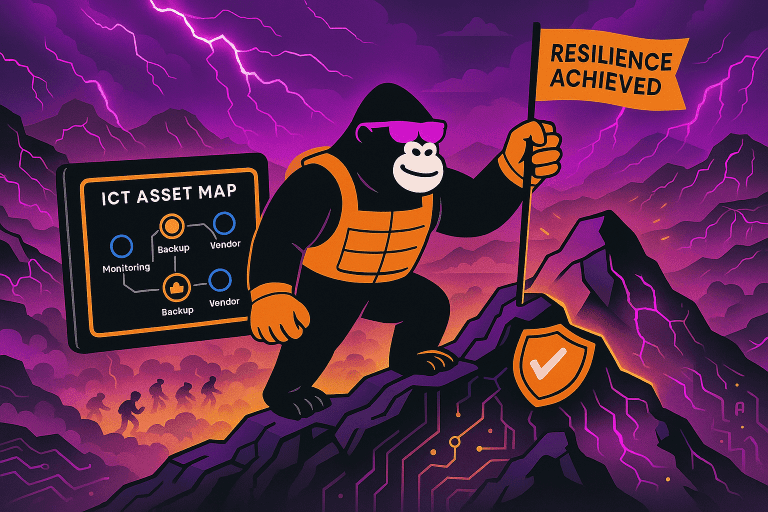
For EU financial institutions and regulated businesses that need SOC 2 as part of a broader compliance programme — alongside ISO 27001, DORA, or NIS2 — Copla provides cross-framework architecture that maps SOC 2 Trust Services Criteria to overlapping requirements across all applicable frameworks from a single connected system. Copla’s central control mapping and multi-framework support allow evidence collected for SOC 2 to be automatically applied to other frameworks like ISO 27001 and HIPAA, eliminating duplicate evidence collection. Updates to one control are reflected across all relevant frameworks, streamlining compliance workflows. Evidence collected for SOC 2 access management controls satisfies ISO 27001 Annex A A.9 and DORA’s access control requirements simultaneously.
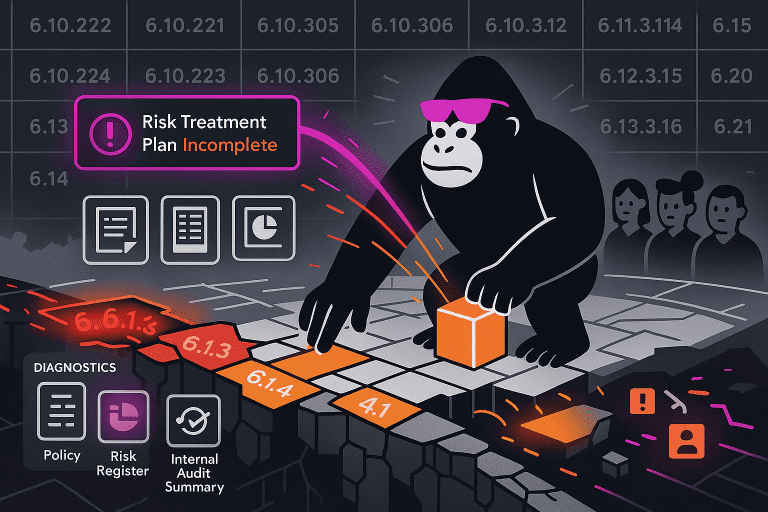
The risk-first approach produces SOC 2 documentation that is more defensible than framework-first platforms — the rationale for each control, connected to the risk assessment that justified it, is maintained in the platform rather than added as a narrative after the fact. The consultancy layer supports SOC 2 audit preparation alongside DORA and ISO 27001 engagements.
Best for: EU financial institutions and regulated businesses needing SOC 2 as part of a multi-framework compliance programme that includes DORA or ISO 27001.
What sets it apart: Cross-framework architecture, risk-connected documentation, and expert support across multiple concurrent frameworks.
Limitations: For standalone SOC 2-only programmes without EU regulatory obligations, Vanta or Drata provide faster paths to first certification.
2. Vanta — Best for Fast SOC 2 Certification
Vanta is the market reference for SOC 2 automation — the platform that defined what good looks like for cloud-native SaaS companies pursuing first and ongoing SOC 2 certification. Its 400+ integrations cover the tech stacks of virtually all SaaS companies, and its auditor partnerships with the major SOC 2 firms mean many audit cycles are managed end-to-end within the Vanta workflow. For companies prioritising speed to Type I and ongoing Type II maintenance, Vanta is the default choice.
Best for: Growth-stage SaaS companies pursuing SOC 2 Type I and Type II for the first time and maintaining continuous readiness.
What sets it apart: Vanta’s extensive integration capabilities, with an ecosystem of over 400 integrations, streamline workflows by connecting seamlessly with cloud services, HR tools, and security solutions. It performs hourly automated checks on more than 1,200 controls, providing real-time visibility into compliance status and enabling organizations to proactively identify and address issues. Its integration breadth, auditor partnerships, and high-frequency continuous monitoring quality make it ideal for fast-moving companies needing quick compliance.
Limitations: Framework-first; risk documentation depth is limited. Pricing from $7,500/year before scaling. DORA and NIS2 support is limited.
3. Drata — Best for SOC 2 Continuous Monitoring
Drata’s real-time control monitoring catches failures as they occur rather than at the next scheduled check — which matters for Type II, where any gap in control effectiveness during the monitoring period is a potential finding. Its integration ecosystem is comparable to Vanta’s, and its cross-framework mapping to ISO 27001 and HIPAA reduces duplicate work for organisations managing multiple frameworks simultaneously.
Best for: Fast-growing companies maintaining SOC 2 Type II alongside other frameworks with a focus on continuous assurance.
What sets it apart: Drata streamlines compliance workflows and manages compliance data across multiple frameworks, including ISO 27001, GDPR, and HIPAA. Its real-time monitoring quality, clean evidence organisation, and cross-framework deduplication enable efficient compliance management and automation.
Limitations: Setup requires configuration investment. Custom enterprise pricing can be high for smaller teams.
4. Scytale — Best for SOC 2 With Dedicated Expert Support
Scytale pairs compliance automation with dedicated GRC experts — not just documentation and tooling, but people who manage the audit timeline, handle auditor communication, and resolve the interpretation questions that software cannot answer. For SaaS companies pursuing SOC 2 for the first time without an internal compliance function, the expert-led model reduces the risk of avoidable audit findings significantly.
Best for: SaaS startups and mid-market companies pursuing SOC 2 for the first time who want expert guidance built into the engagement.
What sets it apart: Scytale guides users through the entire compliance journey and audit process by combining AI-powered automation with dedicated compliance experts. This approach streamlines evidence collection, control monitoring, and documentation, ensuring comprehensive support and a smoother, less stressful audit experience.
Limitations: DORA and NIS2 depth is limited; primarily designed for the SaaS certification market.
5. Secureframe — Best for SOC 2 Alongside Multiple Other Frameworks
Secureframe’s multi-framework coverage and accessible onboarding make it a strong choice for organisations managing SOC 2 alongside ISO 27001, HIPAA, and PCI DSS simultaneously. The account manager model provides human support for organisations navigating multiple compliance obligations without dedicated compliance staff. Its pre-built policy templates and framework crosswalks reduce the interpretation burden for first-time compliance programmes.
Best for: SaaS companies and financial services businesses managing SOC 2 alongside multiple other frameworks.
What sets it apart: Multi-framework breadth, account manager support, and 150+ cloud service integrations.
Limitations: Some users report that support is reactive rather than proactive during audit windows. Starting price around $9,000/year.
6. Sprinto — Best for Fast-Track SOC 2 for Startups
Sprinto markets itself on speed — getting companies audit-ready for SOC 2 in 60 days for focused teams. Its entity-level monitoring tracks individual cloud assets and maps them to SOC 2 controls, providing granular visibility that template-heavy platforms lack. For seed-to-Series-B companies facing a customer deadline for a SOC 2 report, Sprinto’s focus on speed and its competitive startup pricing (from $8,000–$15,000/year) make it the most accessible option.
Best for: Early-stage SaaS companies pursuing first SOC 2 Type I or Type II under customer-driven timeline pressure.
What sets it apart: Speed to first certification, entity-level monitoring, and competitive startup pricing.
Limitations: Rigid workflow structure creates friction for organisations with existing processes. EU regulatory framework depth is limited.
7. Hyperproof — Best for SOC 2 in Mature Multi-Framework Programmes
Hyperproof is designed to support compliance teams managing complex compliance workflows across distributed teams. Its strength is programme management — assigning control ownership, tracking evidence requests, and coordinating evidence collection across distributed teams. For larger organisations managing SOC 2 alongside five or more other frameworks with multiple internal stakeholders owning different control areas, the workflow management layer reduces the coordination overhead that makes large compliance programmes difficult to manage without dedicated GRC staff.
Best for: Mid-to-large organisations with mature compliance programmes managing SOC 2 alongside multiple other frameworks.
What sets it apart: Programme management depth, control ownership tracking, support for compliance teams, and cross-framework evidence reuse to streamline compliance workflows.
Limitations: Less automation than Vanta or Drata; organisations wanting automated evidence collection may find Hyperproof requires more manual input.
8. Thoropass (formerly Laika) — Best for Bundled SOC 2 Software and Auditor
Thoropass bundles GRC software with access to CPA audit partners — the same platform manages compliance preparation and connects you to the auditor, removing one vendor relationship from the process. For companies that want to simplify the audit engagement by working with a single provider, the bundled model reduces coordination complexity. The tradeoff is reduced flexibility in auditor choice.
Best for: Companies that want their compliance software and SOC 2 auditor relationship managed through a single provider, especially those seeking vendor consolidation in compliance tools.
What sets it apart: Thoropass includes vendor risk management features and an integrated audit firm, making it ideal for organizations looking to consolidate vendors. The software plus bundled auditor access eliminates the vendor handoff between compliance preparation and audit.
Limitations: Auditor lock-in reduces flexibility. For companies with established auditor relationships or preferred audit firms, the bundled model provides less value.
Access Reviews and Compliance
Access reviews are a fundamental requirement for SOC 2 compliance, ensuring that only authorized users have access to sensitive systems and data. SOC 2 compliance software simplifies and automates the access review process, reducing manual effort and supporting continuous compliance. Key features include:
- Automated access reviews: SOC 2 compliance software automatically collects and organizes user access data, enabling efficient user access reviews and ensuring that only approved personnel have access to critical systems.
- Continuous monitoring: Real-time monitoring of user access helps organizations quickly identify and remediate security gaps, supporting ongoing compliance with SOC 2 requirements.
- Audit-ready documentation: The platform generates and stores audit-ready documentation for access reviews, making it easy to demonstrate compliance during audits and reducing the risk of findings related to access controls.
By automating user access reviews and providing continuous oversight, SOC 2 compliance software helps organizations maintain compliance, minimize manual effort, and close security gaps related to user access.
How to Choose
For SOC 2-only programmes at cloud-native SaaS companies, the choice is primarily between Vanta, Drata, and Scytale — differentiated by monitoring depth, expert support model, and auditor integrations. The right SOC 2 compliance software should turn SOC 2 from a compliance burden into a growth enabler, providing real-time visibility into compliance status and audit readiness. All three produce good outcomes for their target market.
For organisations managing SOC 2 alongside ISO 27001, DORA, or NIS2, the cross-framework architecture becomes the deciding factor. Running SOC 2 in a separate platform from your EU regulatory compliance programme creates duplicated evidence sets, inconsistent documentation, and a compliance burden that grows faster than the business. A platform that maps SOC 2 controls to ISO 27001 and DORA from a single connected system eliminates that duplication.
Best Practices for SOC 2 Compliance
To maximize the effectiveness of your SOC 2 compliance program, organizations should follow these best practices:
- Implement a compliance automation platform: Use SOC 2 compliance software to streamline compliance management, reduce manual effort, and improve audit readiness.
- Conduct regular risk assessments: Ongoing risk assessments help identify and address security gaps, ensuring your organization maintains compliance with evolving industry standards.
- Maintain continuous monitoring: Leverage continuous monitoring features to detect and remediate compliance issues in real time, supporting ongoing compliance and a strong security posture.
- Provide ongoing training and awareness: Regular training ensures that employees understand SOC 2 compliance requirements and their role in maintaining compliance.
- Review and update security policies: Periodically review and update security policies to reflect changes in compliance requirements and best practices, ensuring your organization remains audit ready.
By following these best practices and leveraging the capabilities of SOC 2 compliance software, organizations can simplify compliance management, maintain a strong security posture, and ensure ongoing audit readiness.
SOC 2 compliance software has made the certification process accessible to organisations that would previously have required a consulting engagement to achieve it. The risk is that accessibility has created a generation of SOC 2 reports backed by evidence packages that are thorough enough to satisfy a standard audit but not deep enough to reflect a genuinely secure and compliant programme. The organisations that get the most value from SOC 2 compliance software are those that use it to build programmes that are actually secure — not just those that produce a report that says so.
FAQ
- SOC 2 compliance helps build consumer trust and can serve as a ‘trust badge’ for business growth, especially for SaaS companies, managed service providers, and organizations handling large amounts of sensitive customer data.
- SOC 2 compliance is not legally required for every business but is often necessary to demonstrate security compliance and a commitment to protecting sensitive data, which strengthens credibility with clients and partners.
How Copla Supports SOC 2 Programmes
We manage SOC 2 compliance as part of multi-framework programmes for EU financial institutions — connecting SOC 2 evidence to ISO 27001 and DORA requirements from a single connected system so the work you do for one framework satisfies the overlapping demands of the others.
Schedule a call with Copla to discuss your compliance programme.
FAQ
-
What is the difference between SOC 2 Type I and Type II? +
SOC 2 reports are based on the trust service criteria developed by the AICPA, which include security, availability, processing integrity, confidentiality, and privacy. SOC 2 Type I attests that security controls are suitably designed as of a specific date — a snapshot. Type II attests that controls operated effectively over a monitoring period, typically six to twelve months, and verifies that systems perform their tasks accurately and completely (processing integrity). Enterprise customers increasingly require Type II reports because they demonstrate ongoing effectiveness rather than a point-in-time state. Most companies pursue Type I first to demonstrate initial readiness, then move to Type II.
-
How long does SOC 2 compliance take? +
Type I typically takes six to twelve weeks from starting a compliance platform to completing the audit. Type II requires a monitoring period of at least six months before the audit can be completed. For focused teams using a well-configured compliance platform, Type I in eight to twelve weeks is realistic. Achieving SOC 2 compliance can significantly improve a company’s data security posture and help prevent costly data breaches by enhancing security measures. Organisations with unusual infrastructure, complex custom environments, or limited internal ownership will take longer.
-
Do I need SOC 2 and ISO 27001? +
SOC 2 compliance is essential for businesses handling sensitive data, such as SaaS companies and managed service providers. Many regulated organisations benefit from both: SOC 2 is primarily a US market signal; ISO 27001 is the European standard. For EU financial institutions with US customers, or US-headquartered companies with EU regulatory obligations, both certifications serve different audiences and are not redundant. A compliance platform that maps both frameworks from a shared control library and evidence set is more efficient than maintaining two separate programmes.