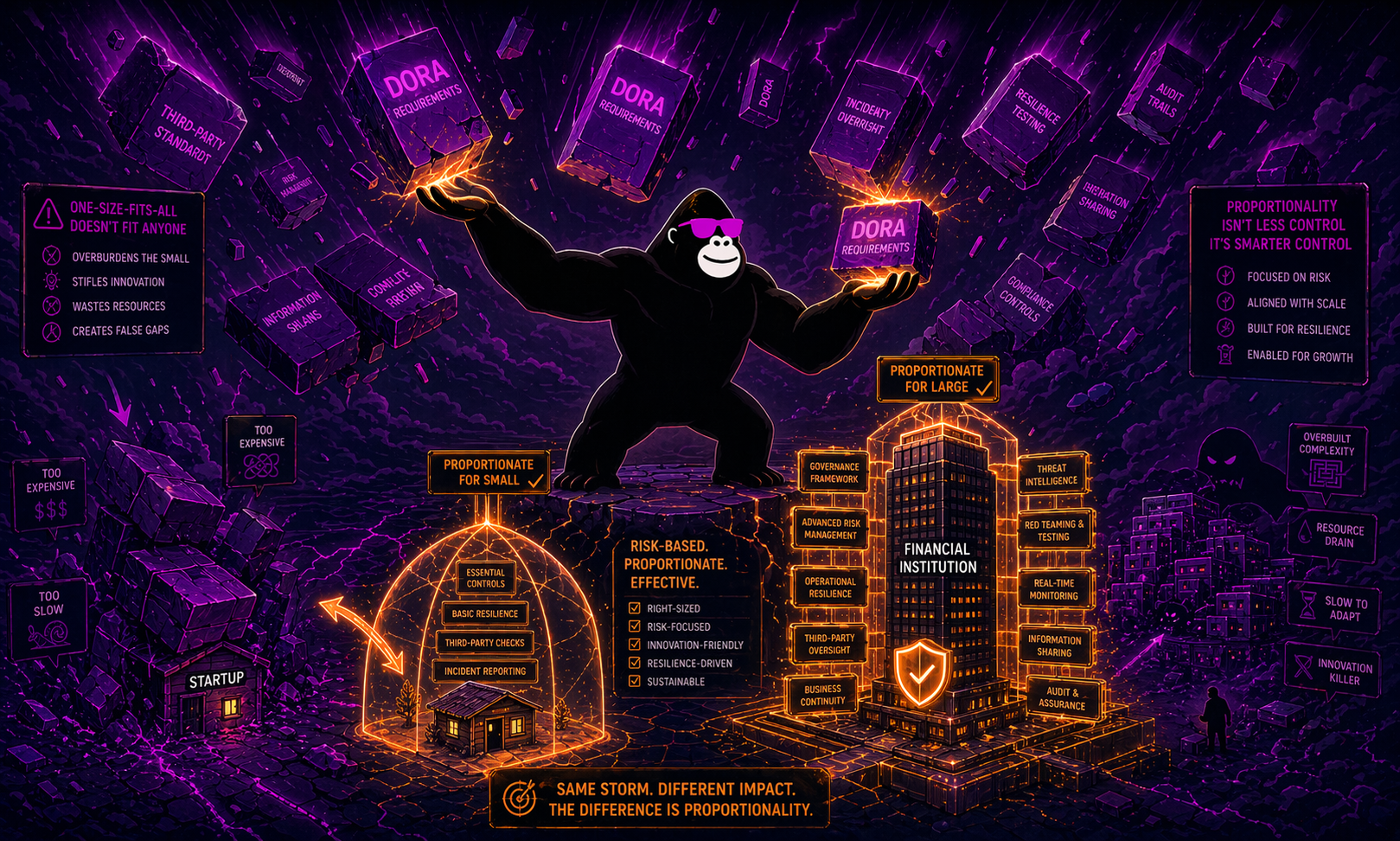
If you work in financial services and the words “DORA compliance” make your stomach drop, I want to offer you something useful: relief. The Digital Operational Resilience Act (DORA), Europe’s landmark regulation on ICT (information and communication technology) risk management for the financial sector, is not a one-size-fits-all rulebook.
Built into its very text is a principle designed to stop regulators from squashing a ten-person payment firm with the same requirements they give to Deutsche Bank. That principle is called proportionality, and understanding it practically changes everything about how you approach DORA.
What Is the DORA Proportionality Principle?
Article 4 of Regulation (EU) 2022/2554 is short. Deceptively short. Financial entities shall implement the rules laid down in Chapter II in accordance with the principle of proportionality, taking into account their size and overall risk profile, and the nature, scale, and complexity of their services, activities, and operations. The same proportionate logic then extends to Chapters III, IV, and V, Section I, which cover incident management, digital resilience testing, and ICT third-party risk management, respectively.
In plain terms: you must comply, but you comply in a way that fits your organization. A community-level credit union does not need the same cyber infrastructure as a systemically important clearing house. What matters is that your measures genuinely mitigate your actual risks. The proportionality principle says that financial entities need to implement reasonable measures only, measures that are proportionate to the organization’s size, business activities, and so on.
The Two-Tier Framework: Full vs. Simplified
This is where proportionality gets concrete. DORA creates two distinct ICT risk management tracks.
The Full ICT Risk Management Framework (Articles 5 to 15)
This is the main regime. It applies to larger, more complex financial entities, including banks, insurance undertakings, investment firms above certain thresholds, central counterparties, and most market infrastructure operators.
Financial entities, other than microenterprises, shall assign the responsibility for managing and overseeing ICT risk to a control function and ensure an appropriate level of independence of such control function in order to avoid conflicts of interest. They must also have their ICT risk management framework reviewed by internal auditors on a regular basis, and review the full framework at least once a year.
The Simplified ICT Risk Management Framework (Article 16)
A range of small and non-interconnected investment firms, payment institutions, electronic money institutions, and small institutions for occupational retirement provision can apply DORA’s Simplified ICT risk management framework. Micro-enterprises, as defined in Article 3(60) of DORA, are also eligible. Under this principle, DORA provides a simplified ICT risk management framework for micro-enterprises and smaller financial entities providing certain services.
The simplified framework still requires you to document and maintain a sound ICT risk management approach, monitor your systems continuously, and handle incidents swiftly. It is not a free pass. The S-RMF does indeed provide some relief from the strict requirements of DORA, but is, in itself, quite austere. What it removes is much of the governance overhead: the mandatory independent control function, mandatory annual audit cycles, and some of the more granular reporting requirements that larger entities face.
Here is a clear comparison of the two tracks:
| Feature | Full Framework (Art. 5-15) | Simplified Framework (Art. 16) |
|---|---|---|
| Who it targets | Large, complex, interconnected entities | Small, non-interconnected firms; micro-enterprises |
| ICT risk framework review | At least once per year | Periodically (and after major incidents) |
| Independent control function | Required | Not required |
| Internal ICT audit | Regular, by qualified auditors | Not explicitly required |
| Third-party ICT risk strategy | Required (Art. 28) | Micro-enterprises exempt (Art. 28(2)) |
| Threat-led penetration testing | Required for designated entities | Generally not applicable |
How Proportionality Works Across DORA’s Five Pillars
Proportionality does not live only in Article 4. It runs through every major pillar of the regulation.
ICT Risk Management
The ICT risk management framework shall be documented and reviewed at least once a year, or periodically in the case of microenterprises, as well as upon the occurrence of major ICT-related incidents. “Periodically” is deliberately flexible. A micro-enterprise can calibrate its review cycle to its risk profile rather than hitting a hard annual deadline.
Incident Reporting
The ESAs ensure that the requirements of the draft RTS and ITS are proportionate and consistent with the approach for incident reporting under Directive (EU) 2022/2555 (NIS 2). The classification of what constitutes a “major” ICT incident is also calibrated to the number of clients impacted and the criticality of the affected services, so smaller entities with narrower exposure are less likely to trigger the full reporting chain.
Digital Operational Resilience Testing
A proportionate, risk-based testing program must be established, which includes vulnerability assessments and scans, open source analyses, network security assessments, gap analyses, physical security reviews, questionnaires, scanning software solutions, source code reviews, as well as compatibility and performance testing. More advanced threat-led penetration testing (TLPT) is only mandated for entities that competent authorities specifically designate based on their overall risk and business profile, typically the largest and most systemically important players.
ICT Third-Party Risk
The principle of proportionality is expressly built into the application of DORA’s contractual requirements based on the nature, scale, and complexity of services. The relevance of specific contract clauses varies by the type of ICT service involved. Microenterprises are not required to develop a third-party ICT risk strategy as part of their ICT risk management framework (Article 28(2)).
Who Decides What Is “Proportionate”?
This is the part that keeps compliance teams up at night, and it deserves an honest answer. The competent authorities shall consider the application of the proportionality principle by financial entities when reviewing the consistency of the ICT risk management framework on the basis of the reports submitted upon the request of competent authorities pursuant to Article 6(5) and Article 16(2). In other words, proportionality is evaluated case by case, by your national supervisor.
The challenge is that there are 27 national competent authorities across the EU. Since there are 27 authorities, one for each member state, there is every chance that we are going to see 27 different interpretations. The European Supervisory Authorities (ESAs), specifically the European Banking Authority (EBA), the European Insurance and Occupational Pensions Authority (EIOPA), and the European Securities and Markets Authority (ESMA), are continuously publishing Q&As and technical standards to improve consistency. But interpretive variation at the national level remains a real factor, especially in the short term.
What This Means in Practice: Three Scenarios
Scenario 1: A small payment institution. You qualify for the simplified framework. You still need a documented ICT risk management framework, continuous monitoring, and incident handling. What you are spared is the mandatory independent control function, the annual internal audit requirement, and the obligation to build a formal third-party ICT risk strategy. You focus on the essentials and document your reasoning clearly.
Scenario 2: A mid-sized investment firm. You likely fall under the full framework. Proportionality still applies within that framework. Your testing program does not need to be as extensive as a major bank’s, and your incident reporting thresholds are calibrated to your actual exposure. You build a risk-based testing plan and document why it is appropriate for your scale.
Scenario 3: A large insurance group. You face the full framework with minimal flexibility on governance requirements. However, proportionality still shapes how you design individual controls and calibrate your digital resilience strategy across subsidiaries of different sizes. A micro-enterprise subsidiary might qualify for the simplified track even if the parent does not.
The Golden Rule: Document Everything
It will be crucial for financial entities to ensure they implement DORA proportionately and on a reasonable and justified basis, adopting a properly documented risk-based approach to withstand regulatory challenges. I cannot stress this enough. Proportionality without documentation is just non-compliance with good intentions. Every decision you make about the scope, depth, and frequency of your ICT controls needs a paper trail that explains why it is appropriate for your size and risk profile.
Financial entities must also ensure they do not go beyond what is proportionate and necessary by implementing superfluous and onerous procedures that incur avoidable costs. Over-compliance is a real risk too. Implementing controls you do not need wastes resources and can create operational complexity that actually undermines resilience rather than supporting it.
To ensure compliance withstands FSA scrutiny, thorough documentation of the interpretation of the requirement depth is recommended. Leverage the overall proportionality principle and tailor the requirements according to the organization’s size, complexity, interconnectedness, and potential risk exposure.
Your Next Steps
DORA has been live since January 17, 2025. If you have not already mapped your entity to the correct framework tier, that is the first task. From there, the practical path looks like this:
- Confirm whether you qualify for the simplified framework under Article 16 or fall under the full regime.
- Conduct a gap analysis calibrated to your specific tier and risk profile, not a generic DORA checklist built for a large bank.
- Document every design decision in your ICT risk management framework, especially where you have exercised proportionality to adopt a lighter-touch control.
- Monitor ESA guidance. The technical standards are still evolving, and new Q&As are being published that directly affect how proportionality is interpreted across different entity types.
- Engage your national competent authority early if you are uncertain about how your framework will be assessed.
DORA is serious regulation. It is also, by design, a regulation that acknowledges not every financial entity carries the same systemic risk. Use that acknowledgment to your advantage.