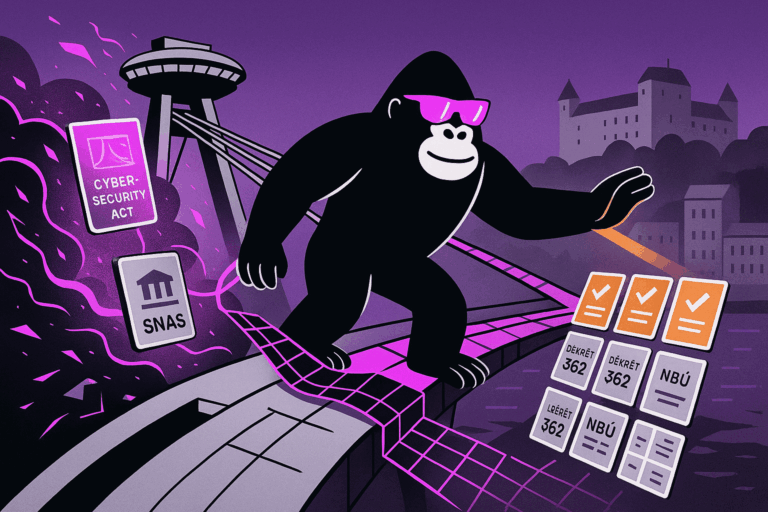
Regulators now require the EU’s largest financial institutions to let ethical hackers attack their live banking systems. That is not a drill. The Digital Operational Resilience Act (DORA), Regulation (EU) 2022/2554, mandates a program called Threat-Led Penetration Testing (TLPT)—full-scale, intelligence-driven cyberattack simulations on real production systems —at least once every three years.
As of July 8, 2025, the Commission Delegated Regulation (EU) 2025/1190 — the Regulatory Technical Standards (RTS) that fills in every operational detail — is live and directly applicable across all EU member states.
Here is what DORA TLPT actually requires, who it applies to, and how to prepare.
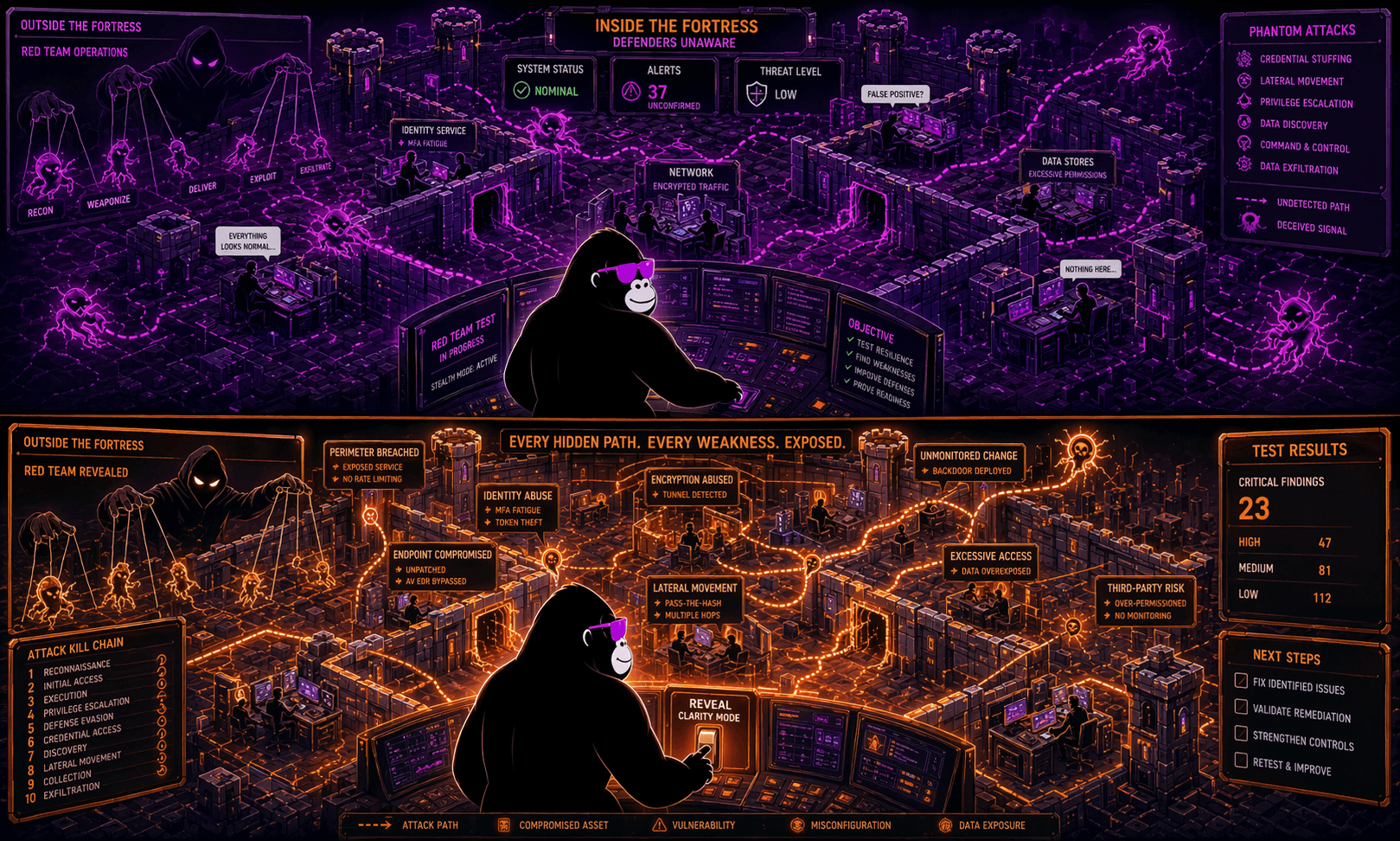
TLPT Is Not a Penetration Test
This distinction matters more than most people realize, so let me be direct.
A conventional penetration test scopes one application or network segment, runs for a week or two, and produces a vulnerability list. The security team knows it is happening.
TLPT is a full-scale red team exercise on live production systems, based on real threat intelligence specific to your sector. The Blue Team — your defensive security staff — has no idea the test is happening. That covert setup is the point: you are measuring genuine operational resilience, not a rehearsed response.
The concept traces back to the ECB’s TIBER-EU framework (Threat Intelligence-Based Ethical Red Teaming for the European Union), which launched in 2018 as a voluntary program. DORA makes it mandatory for systemically important institutions. In February 2025, the ECB updated TIBER-EU to fully align with DORA’s RTS, meaning that completing a TIBER-EU test under the updated guidance satisfies DORA TLPT requirements.
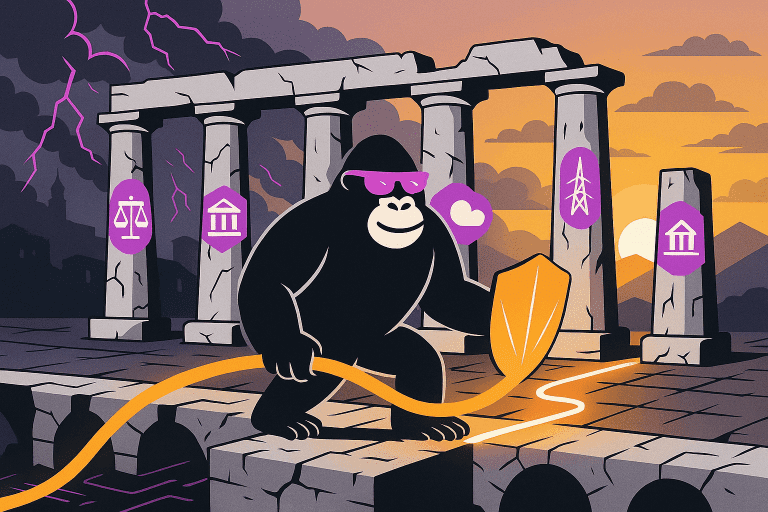
Who Must Conduct TLPT
DORA does not require every financial entity to run TLPT. Article 26(1) of DORA and Article 2 of the RTS target institutions whose failure could genuinely destabilize the EU financial system.
Mandatory scope includes:
- Systemically important credit institutions — Global Systemically Important Institutions (G-SIIs) and Other Systemically Important Institutions (O-SIIs) classified under Article 131 of Directive 2013/36/EU
- Large payment and electronic money institutions — those that processed more than €150 billion in total transactions in each of the two preceding years
- Additional designated entities — national competent authorities may designate other financial entities, including insurers, investment firms, crypto-asset service providers (CASPs), and critical ICT third-party service providers, based on risk profile and systemic importance
You do not self-select for TLPT. Your national TLPT Authority sends a formal notification letter when you are in scope. The first wave of notifications is expected in 2026.
TLPT vs. Annual Testing
DORA establishes two testing tracks. Confusing them is a common mistake.
| Annual Testing (Articles 24–25) | Advanced TLPT (Article 26) | |
|---|---|---|
| Who | All DORA-covered entities | Designated significant entities only |
| Frequency | At least annually | At least every 3 years |
| Scope | Critical ICT systems | Live production systems, all critical functions |
| Blue team aware? | Yes | Never |
| Threat intelligence | Not required | Always external |
| Output | Remediation report | Formal regulatory attestation |
Annual testing — vulnerability assessments, network reviews, application penetration tests, scenario exercises — applies to every DORA-covered entity and remains mandatory regardless of TLPT designation.
The Key Participants
- TLPT Authority: The designated national authority that identifies in-scope entities, approves scope documents, oversees the exercise, and issues the formal attestation. Each member state designates one under Article 26(9) or delegates authority under Article 26(10).
- Control Team: A small internal team within the financial entity that manages the entire process — coordinating with the Authority, hiring providers, and maintaining strict confidentiality from the Blue Team. The Control Team Lead is a named individual accountable to the Authority.
- Threat Intelligence (TI) Provider: Always external. They analyze the adversarial landscape relevant to your sector and develop the attack scenarios the Red Team will execute.
- Red Team: The ethical hackers who execute attacks on live systems. Internal testers are permitted under DORA — a departure from original TIBER-EU — but with conditions (see below).
- Blue Team: Your defensive security staff. They must remain completely unaware of the test throughout the entire active phase.
Internal vs. External Testers: The Actual Rules
Three conditions govern who can conduct the red teaming:
- The TI Provider must always be external, regardless of who does the red teaming.
- If you use internal testers for two consecutive TLPTs, the third must use an external Red Team.
- Credit institutions under direct ECB supervision must always use external testers — no internal option.
External providers must meet minimum qualifications: the Red Team Lead needs at least 5 years of penetration testing experience, supporting members need at least 2 years each, and the team must have at least 3 prior assignments in threat intelligence and red team testing.
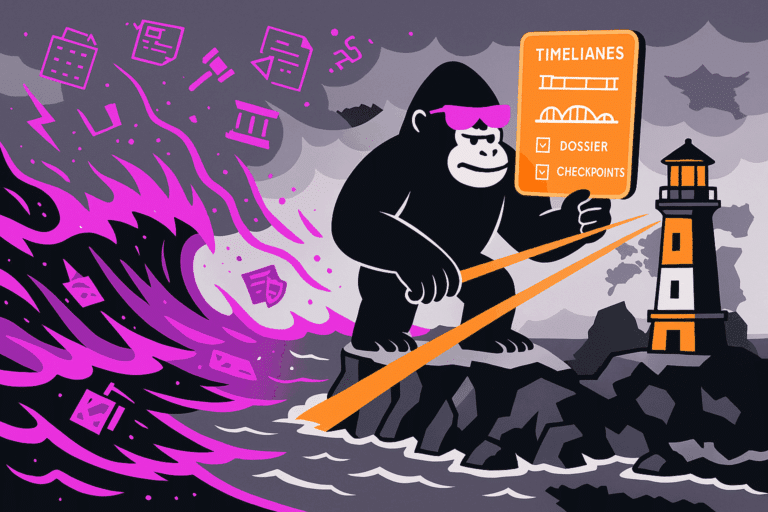
The TLPT Process: Notification to Attestation
The full engagement realistically runs six to twelve months. Here is how it breaks down.
- Initiation (0–3 months from notification): Submit a high-level project plan, name your Control Team Lead, and confirm communication protocols with the TLPT Authority.
- Scoping (0–6 months from notification): Submit a detailed Scope Specification Document mapping every critical or important function (CIF), the underlying ICT systems, and the defined targets a real adversary would pursue. The TLPT Authority approves this document before testing begins.
- Threat Intelligence: The external TI Provider develops realistic attack scenarios based on adversaries relevant to your institution and sector.
- Active Red Team Phase: The Red Team executes scenarios on live production systems while the Blue Team remains unaware. The Control Team monitors for situations requiring a pause — actual incidents or risk of genuine data corruption.
- Closure and Purple Teaming: DORA makes purple teaming mandatory in the closure phase. The Red Team and Blue Team review each attack scenario together, with the Blue Team now fully informed. This structured knowledge transfer is one of DORA’s most significant departures from earlier frameworks, which only recommended it. A test that produces documentation but no organizational learning is not worth the cost.
- Reporting and Attestation: The financial entity submits findings, a remediation plan, and compliance documentation. The TLPT Authority issues a formal attestation. Under Article 26(7) of DORA, that attestation enables mutual recognition across EU member states — one attestation can satisfy supervisory requirements in multiple jurisdictions.
Third-Party ICT Providers Cannot Opt Out
Article 30(3)(d) of DORA requires financial entities to include TLPT cooperation obligations in outsourcing agreements with third-party ICT service providers. If a critical function has been outsourced to a cloud provider or data analytics firm, that vendor must participate in the scope of the test. Under Germany’s voluntary TIBER-DE program, many providers refused to cooperate. DORA removes that option. Refusal is no longer legally viable for providers whose contracts include the required DORA clauses — and regulators expect those clauses to be in place.
What to Do Before the Notification Letter Arrives
Map your critical and important functions now. The Scope Specification Document demands a detailed inventory of every CIF and its supporting ICT systems, including outsourced and cloud-based dependencies. This work consistently takes longer than organizations expect.
- Identify your Control Team Lead. This person will be named to the TLPT Authority and needs the seniority, regulatory literacy, and authority to manage external providers — often under conditions of strict internal confidentiality.
- Audit your third-party contracts. Add TLPT cooperation obligations to outsourcing agreements now, not under time pressure once scoping begins.
- Vet your providers early. Qualified TI Providers and Red Teams meeting DORA’s minimum criteria are not numerous. Offensive security credentials such as OSCP, OSEP, and CRTO are the practical benchmark for Red Team members. Start evaluating before your notification arrives.
- Budget realistically. A full TLPT engagement runs to hundreds of thousands of euros for complex institutions. Build this into your 2026 and 2027 budget cycles.
TLPT is the EU regulator’s answer to a direct question: do the financial institutions that underpin the European economy hold up under real attack conditions? Before DORA, that was taken on faith. Now you have to demonstrate it. The path to compliance is demanding but entirely navigable — and the earlier you start, the better positioned you will be when that notification letter lands.