If you work in EU financial services and someone drops “TLPT” into a meeting, you need to know exactly what it means for your organization. Not in a vague, hand-wavy way. In a “do we need to do this, when, and what does it actually involve” kind of way. That is what this article is for.
Let me break down the Threat-Led Penetration Testing (TLPT) scope under the Digital Operational Resilience Act (DORA) — Regulation (EU) 2022/2554 — and give you the clearest picture possible of who is in scope, what the test covers, and how the whole process works.
What Is DORA TLPT, and Why Does It Exist?
DORA is a regulation passed by the European Parliament and Council in December 2022. Its goal is simple: make sure financial entities in the EU can withstand, respond to, and recover from ICT (information and communication technology) disruptions and cyberattacks.
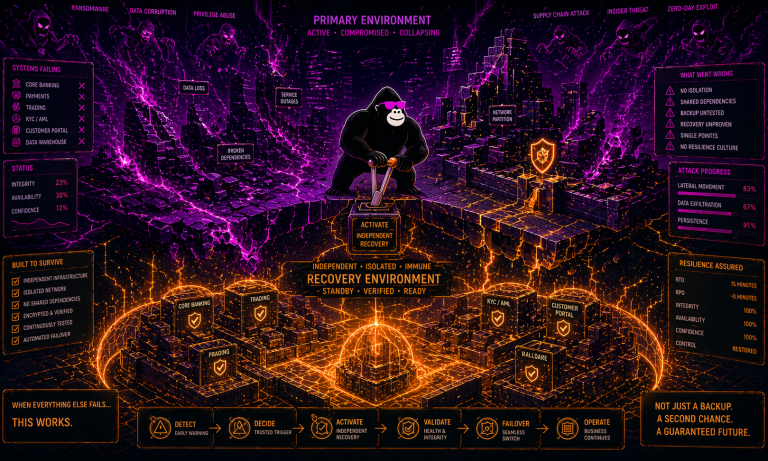
TLPT is one of DORA’s most demanding requirements. Article 3(17) of the regulation defines it as a framework that “mimics the tactics, techniques and procedures of real-life threat actors perceived as posing a genuine cyber threat.” In plain English: it is a controlled, intelligence-led cyberattack simulation run against your live systems, carried out by skilled red team testers who are simulating an actual adversary.
This is not a standard penetration test. A standard pentest scopes one application or network segment, takes a week or two, and produces a list of vulnerabilities. The security team knows it is happening. TLPT, by contrast, is covert. The organization’s defensive team — the blue team — does not know a test is underway. The red team has weeks or months to operate and must attempt to reach pre-defined targets (called “flags”) by any realistic means: phishing, social engineering, physical intrusion, and network attacks alike.
The legal basis for TLPT requirements sits in Article 26 of DORA. The detailed technical rules are set out in Commission Delegated Regulation (EU) 2025/1190, which was published in the Official Journal on June 18, 2025, and came into force on July 8, 2025.
Who Is in Scope for DORA TLPT?
This is the question most compliance teams want answered first. The honest answer: not everyone. DORA explicitly limits TLPT to the largest, most systemically critical financial entities in the EU.
Article 26(8) of DORA instructs competent authorities — referred to as TLPT Authorities — to identify which financial entities must perform TLPT, based on three factors: the entity’s impact on financial stability, possible systemic concerns, and the specific ICT risk profile and maturity of the entity.
Article 2 of Delegated Regulation (EU) 2025/1190 then sets out specific entity-by-entity criteria. The mandatory TLPT population includes:
| Entity Type | Key Threshold |
|---|---|
| Credit institutions | Identified as Global Systemically Important Institutions (G-SIIs) or Other Systemically Important Institutions (O-SIIs) under Directive 2013/36/EU |
| Payment and electronic money institutions | Entities exceeding defined transaction volume thresholds |
| Trading venues (stock exchanges, MTFs) | Holding the highest national market share in key instrument categories or accounting for more than 5% of EU-level trading turnover |
| Central counterparties (CCPs) | All entities authorized under EMIR |
| Insurance and reinsurance undertakings | A specific subset meeting gross written premium thresholds above €1.5 billion, technical provisions above €10 billion, and total assets exceeding 3.5% of the national sector, plus at least one elevated threshold |
Even if your entity meets all the numerical criteria above, your national TLPT Authority can still exempt you if the assessment shows your ICT risk profile does not justify a full TLPT. The reverse is also true: if you fall outside these categories but the regulator considers you a meaningful systemic risk, they can designate you as in scope.
For group structures, TLPT Authorities coordinate across borders to determine whether individual subsidiaries need separate tests or whether a group-level test suffices.
What Does the TLPT Scope Actually Cover?
Once your organization is identified as in scope, Article 26(2) of DORA specifies what the test must cover. The TLPT must encompass “several or all critical or important functions” of the financial entity, and it must be performed on live production systems — not sandboxed environments or replicas.
You are required to identify all relevant underlying ICT systems, processes, and technologies that support those critical or important functions. That identification must extend to any ICT services outsourced to third-party providers. Where third-party ICT service providers are included in the scope, the financial entity must take the necessary measures to secure their participation in the test.
This is a significant operational requirement. It means that a TLPT is not a closed-door exercise between your security team and a red team vendor. It may require coordinating with cloud providers, data processing partners, and other critical ICT suppliers.
The scope is formally documented in what is called a Scope Specification Document (SSD). After a TLPT Authority sends a notification letter to an in-scope entity, the entity has three months to submit initial planning documents and six months to submit the full SSD, which must detail the critical and important functions, the underlying systems, and the defined flags.
How TLPT Connects to TIBER-EU
You cannot understand DORA TLPT without knowing what TIBER-EU (Threat Intelligence-Based Ethical Red Teaming for the EU) is. TIBER-EU is the European Central Bank’s framework for conducting threat intelligence-led red team testing across the financial sector. It was first introduced in 2018 and has since been adopted across 16 or more EU member states through national implementation guides.
DORA’s Article 26(11) explicitly requires the European Supervisory Authorities — the European Banking Authority (EBA), European Insurance and Occupational Pensions Authority (EIOPA), and European Securities and Markets Authority (ESMA) — to develop the TLPT technical standards “in accordance with the TIBER-EU framework.” On February 11, 2025, the ECB updated the TIBER-EU framework to formally align with DORA’s Regulatory Technical Standards, meaning the two are now substantively harmonized.
If your jurisdiction has a national TIBER-EU implementation, you can use that framework to conduct and satisfy your DORA TLPT obligations, as long as any additional DORA-specific requirements are incorporated.
The Testing Process: Six Phases in Practice
A DORA TLPT follows a structured lifecycle. Here is how it works in practice.
- Phase 1 — Preparation. The TLPT Authority assigns a TLPT Cyber Team (TCT), which acts as the supervisory body coordinating the test. The financial entity forms a Control Team (previously called the White Team in TIBER-EU), selects its Threat Intelligence Provider (TIP) and Red Team Tester (RTT), and begins the scoping process.
- Phase 2 — Threat Intelligence. The TIP, who must always be external to the tested entity, develops a Threat Intelligence (TI) report based on the specific threat landscape relevant to your organization and sector. This report directly shapes the red team’s attack scenarios.
- Phase 3 — Red Teaming. The red team executes the attack simulation against live production systems, guided by the TI report. This phase typically runs for several months, with the blue team unaware of the ongoing exercise.
- Phase 4 — Closure and Purple Teaming. Once the red team completes its exercise, a purple teaming phase is mandatory under Delegated Regulation (EU) 2025/1190. This is a collaborative replay session in which red and blue teams work together to walk through what happened, what worked in the attacker’s favor, and where defenses held. Purple teaming was previously encouraged but not required under the original TIBER-EU framework. DORA has made it compulsory.
- Phase 5 — Reporting. The financial entity and, where applicable, the external testers submit a summary of findings and remediation plans to the designated authority.
- Phase 6 — Attestation. Article 26(7) of DORA requires the TLPT Authority to issue a formal attestation confirming the test was conducted in accordance with requirements. This attestation enables mutual recognition between EU member states, so organizations operating across borders do not have to repeat the full exercise for each national regulator.
Internal vs. External Testers: What DORA Allows
DORA introduces a notable departure from the original TIBER-EU framework. Article 26(8) of DORA allows financial entities to use internal red team testers — something TIBER-EU previously did not permit.
However, there is a clear safeguard: entities that use internal testers must contract fully external testers for every third TLPT. The Threat Intelligence Provider must always be external, regardless of who performs the red team role. This ensures that a degree of independence and objectivity is maintained even when organizations use their own red team resources for cost or operational reasons.
How Often Must TLPT Be Performed?
Article 26(1) of DORA sets the baseline: at least every three years. A competent authority can shorten or lengthen that interval based on the entity’s specific risk profile and operational circumstances. Given that DORA became applicable in January 2025, and that TLPTs are substantial undertakings requiring months of preparation and execution, the first wave of completed DORA TLPTs is expected to occur in late 2026 through 2027.
Practical Steps to Take Now
If your organization may fall within scope or is awaiting confirmation from its national TLPT Authority, there are concrete things you can do right now.
Start by mapping your critical and important functions. You need to be able to define clearly which functions would trigger significant operational or financial harm if disrupted. This mapping forms the foundation of the Scope Specification Document you will eventually submit. Identify the underlying ICT systems, processes, and technologies that support those functions, including any third-party providers.
Establish a Control Team Lead. This person will be the primary point of contact with the TLPT Authority and will coordinate the internal response to the test. Their details are among the first things you need to submit after receiving a notification letter.
Begin evaluating qualified external providers. The threat intelligence provider and, if you are using external testers, the red team provider must meet specific qualification requirements under the RTS. You want to have this process well underway before the official clock starts.
Familiarize yourself with the TIBER-EU framework published by the ECB. Since DORA TLPT is built on TIBER-EU, understanding that framework gives you a strong practical head start on what the full testing process will look like.
The Bottom Line
DORA TLPT is the most rigorous cybersecurity testing requirement the EU has ever placed on financial institutions. It is not a bureaucratic checkbox. It is a live-fire exercise designed to expose whether your organization’s defenses can withstand a sophisticated, intelligence-led adversary.
The scope under Article 26 of DORA, as detailed by Commission Delegated Regulation (EU) 2025/1190, is deliberately targeted at the entities whose failure would cause the most harm to financial stability across the EU. If you meet the criteria, a notification letter from your TLPT Authority is a matter of when, not if.
The good news: the framework is well-defined, the TIBER-EU guidance is available and updated, and the timeline gives prepared organizations room to get ready. Start mapping your critical functions, evaluate your provider options, and get your Control Team structure in place. When the letter arrives, you will want to be ready.